Latest News
Decade-Long SniperDz Phishing Network Disrupted in Operation Ramz
Group-IB, INTERPOL and Algerian Police dismantle decade-old SniperDZ phishing network used to steal credentials, with its alleged developer arrested.
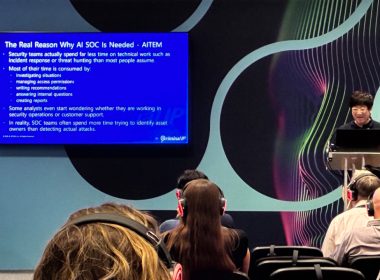
Criminal IP at Infosecurity Europe 2026: Introducing AITEM, the Next Chapter of Attack Surface Management
Torrance, United States / California, 11th June 2026, CyberNewswire
Hackers Use Fake Claude Code Guide and AI PDFs to Spread AsyncRAT Malware
Hackers are using fake Claude Code guide and AI PDFs to spread AsyncRAT malware via Windows attack using PowerShell and Defender exclusions.
The Hidden Security Risks of Poor Software Testing
Poor Software Testing can expose hidden flaws, vulnerable dependencies and weak controls, increasing breach risks, downtime and costly fixes…
FBI Seizes China-Linked Fake Consulting Sites Targeting US Clearance Holders
The Justice Department and FBI seized 13 fake consulting websites that officials say targeted US clearance holders with paid research work…
How to Turn Images into Animated Videos with AI: A Wondershare Filmora Guide
This article was created in collaboration with Wondershare.
Scammers Use TikTok and Instagram Reels to Spread Vidar Infostealer
ReversingLabs reveals how hackers exploit social media engagement metrics to deliver Vidar infostealer malware to thousands of unsuspecting users.
ServiceNow Discloses Security Incident Exposing Customer Data
ServiceNow applied a security update after an API access issue exposed customer data, with affected firms notified through direct support cases.
Cloud Security Report Finds Fragmented Tools Widening the Cloud Complexity Gap
Washington D.C., USA, 10th June 2026, CyberNewswire
Microsoft June 2026 Patch Tuesday Fixes 206 Flaws and 3 Zero-Days
Microsoft’s June 2026 patch Tuesday resolves 206 vulnerabilities, including 3 critical zero-days and severe 9.8 CVSS kernel, network and…
Network Log Analysis: Why Collecting Logs is Not Enough
Network Log Analysis helps teams turn raw logs into useful alerts, timelines, audit records, and incident evidence instead of storing data…
E-Signature Security Checklist Before Selecting an E-Signature Tool
Electronic signature security starts before the first document is sent. A company needs to know how files are encrypted, how signers are…