By 2023, the volume of data generated worldwide had reached 120 zettabytes, and information flows continue to grow exponentially. This surge demands a reassessment of cybersecurity strategies.
The focus is shifting toward protecting data not only within corporate networks but also in the Internet of Things (IoT) space. Increasingly, personal computers and mobile devices are becoming valuable targets for cybercriminals due to the sensitive information they store.
Sultan Omurzakov, Senior Software Engineer at a leading autonomous vehicle company, specialises in developing systems to enhance software security, protect data in machine learning processes, and manage big data. He holds several patents in network security, IoT device protection, and early detection of ransomware.
As a co-author of major projects at Roblox, Palo Alto Networks, Truist, and Deloitte, and a certified CISA member of ISACA, Sultan brings deep expertise in preventive cybersecurity solutions, those that must be developed today to effectively safeguard data in an era of rapid technological advancement. In this exclusive interview, he shared insights into the key directions shaping the future of information security.
Sultan, you recently received a patent for an innovative technology enabling instant detection of ransomware in corporate networks for Palo Alto Networks. What makes it unique?
We moved away from signature-based detection. I began working on this project at Palo Alto Networks in 2021, during the height of the COVID-19 pandemic, when remote work became widespread and cybersecurity challenges intensified. At the time, one of the most serious risks users faced was ransomware attacks, malicious programs that encrypt all data and demand a ransom for its release.
Victims ranged from oil pipeline employees to casinos and even hospitals. While studying these attacks and the available countermeasures, I noticed that many antivirus programs relied on signature detection to identify malicious elements.
A signature is a fragment of a virus’s code, which can be compared to a piece of DNA or RNA used to detect biological viruses. This method is fast and reliable, but once the virus mutates, the protection becomes ineffective. I also observed that some ransomware strains spread across local networks using the Windows Server Message Block (SMB) protocol. That’s when I decided to develop a universal algorithm that wouldn’t rely on signatures.
The idea was to analyse network traffic over the SMB protocol and apply Shannon entropy calculations. This allowed us to detect even polymorphic ransomware variants. The approach was innovative and became part of the product as one of its heuristic detection methods. According to independent tests conducted by Miercom, the Palo Alto Networks cloud firewall detected and blocked 100% of threats, far outperforming Amazon AWS Firewall (4%) and Microsoft Azure Firewall (31%).
One of your other standout innovations is a method for identifying devices behind NAT networks. What kinds of IoT environments is it suited for?
This technology is already being used in healthcare, industrial facilities, and smart buildings. It helps identify which devices are generating traffic within NAT networks. That’s particularly important because it’s common for data from a large number of devices to pass through a single router.
My colleagues and I developed a machine learning–based method that starts by determining whether traffic coming from one router is generated by a single device or multiple ones. Then, we break the traffic into short intervals, classify each “burst,” and run it through a multi-class model. That model determines which devices are likely responsible for each data segment. Using only passive traffic analysis, no expensive sensors, we’re able to identify up to 92% of end devices behind a NAT.
In your security research on an internet-connected camera for Palo Alto Networks Unit 42, you discovered a vulnerability. What was it?
My research, titled “CVE-2021-28372: How a Vulnerability in Third-Party Technology Is Leaving Many IP Cameras and Surveillance Systems Vulnerable,” focuses on the Chinese IoT platform Throughtek Kalay. This platform is used in a large number of IP surveillance cameras across the US and EU, including those sold under American and European brand names.
My colleagues and I discovered a vulnerability in the Kalay cloud that allowed anyone to register any IP camera to their own account. Once the camera was connected to the cloud, full access to the device, including all video recordings, could be obtained. This case demonstrated that even the smallest component in a camera can pose a risk, and it’s essential to have a solution that secures camera network traffic, both incoming and outgoing.
You recently took part in the CES (Consumer Electronics Show) forum. What topics were discussed?
At CES, I participated in a panel focused on the cybersecurity of autonomous systems, from vehicles to household robots. We discussed threats related to self-driving cars and the need to implement secure communication protocols between vehicle components.
There were also sessions on the security of consumer IoT devices, where I shared my experience protecting smart cameras and smart speakers from attacks. Forums like these help us stay at the forefront of progress, exchange expertise with other professionals, see how real companies apply best practices, and keep a finger on the pulse of advancements in security.
You have worked on securing gaming platforms, banks, corporate networks, and developed solutions for machine learning, AI systems, as well as IoT. Is there anything common across these areas?
All these areas are united by one thing: a massive volume of data that needs to be protected. I’m drawn to changing directions because it allows me to broaden my horizons and apply experience from one industry to another. For example, behavioural analysis used in game development, such as detecting cheaters, works very well in analysing network traffic to identify anomalies. Traffic analysis of microservices is applicable to any tech company.
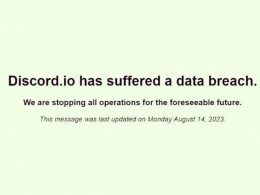
The cybersecurity field faces many challenges, the biggest of which is the impact of AI. Already today, autonomous AI agents rank as the most productive and effective hackers, according to the HackerOne platform.
In the future, this technology is highly likely to fall into the hands of malicious actors, and almost all websites and servers on the Internet will face increased risks of breaches and data leaks. That’s why it’s crucial right now to take enhanced security measures, strengthen system defences, and implement monitoring systems for network attacks and threats.