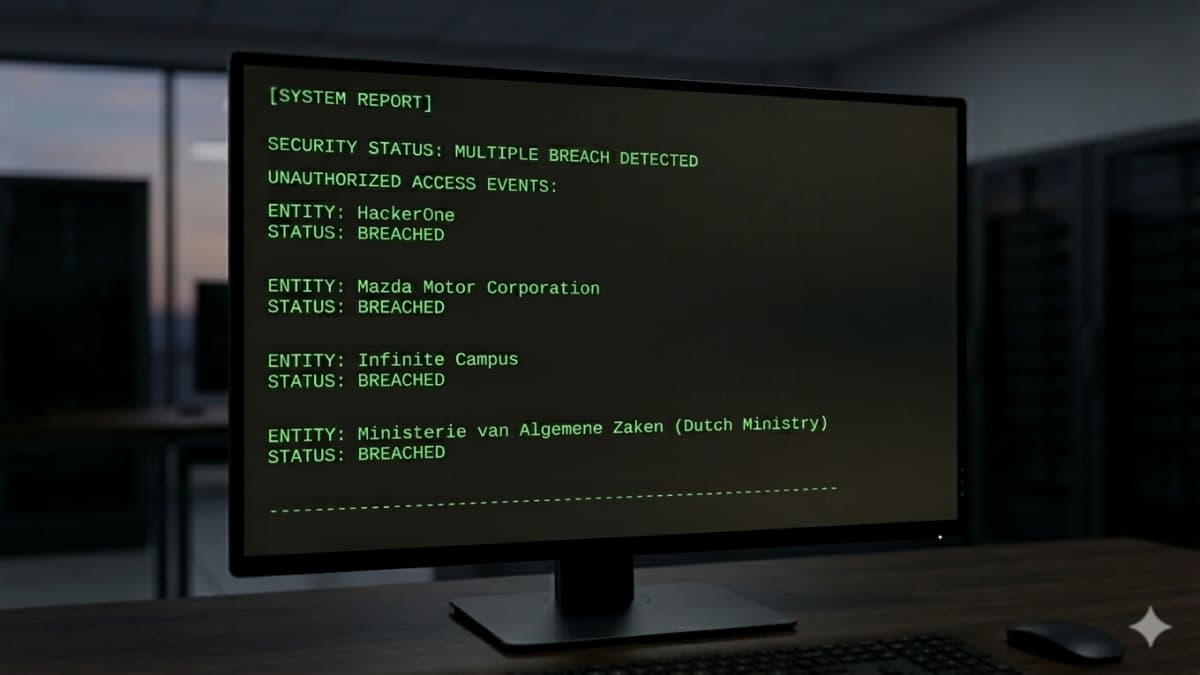
A series of recent data breach disclosures is putting employee data security back into focus, as four separate organizations confirmed or responded to incidents involving internal records and third-party systems. While each case differs in scope, they do share one target, which is employees.
Dutch Ministry of Finance Employee Data Breach
The Dutch Ministry of Finance is the latest government body dealing with that reality. Officials confirmed that employee data was accessed after an internal system was compromised. Early reports indicate the breach exposed personal details of staff, though authorities have not publicly detailed the full dataset.
One detail worth noting is that the breach was spotted from inside the organization rather than flagged by an outside party, which points to some monitoring already in place. Yet, it shows that government systems are being targeted not only for intelligence gathering, but also for collecting employee data.
Infinite Campus Data Breach
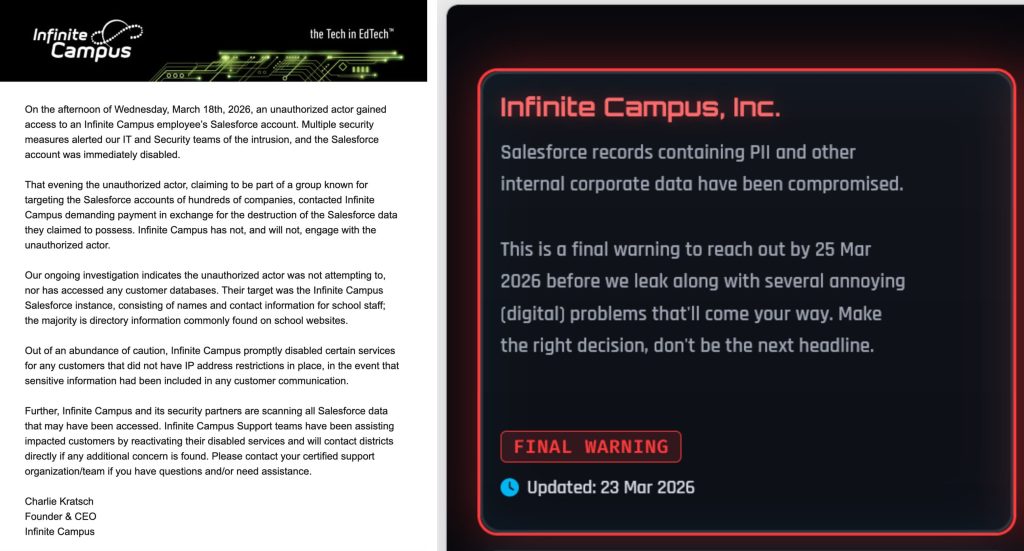
At the same time, education technology provider Infinite Campus is dealing with claims from the ShinyHunters group, which says it exfiltrated data from the company’s systems. Infinite Campus acknowledged unauthorized access but did not disclose the full scale of the breach or whether student records were affected.
However, as reported by Hackread.com, the attackers claim they accessed Salesforce-related data that includes personal and internal corporate information. They are also threatening to leak the data if Infinite Campus does not meet their extortion demands.
HackerOne Data Breach
Another case shows how third-party relationships can expand the impact of a breach. HackerOne disclosed that employee data was exposed following a compromise involving Navia, a vendor that provides benefits administration services. The same service disclosed a data breach last week, revealing 2,697,540 of its users were impacted.
According to the company’s data breach notification filed with Maine’s attorney general’s office, the breach did not originate within HackerOne’s own systems but still resulted in the exposure of staff information handled by the vendor. Incidents like this continue to show that even companies with strong internal security programs remain exposed through external partners.
Mazda Data Breach
Mazda is facing a similar situation, though in a different context. The automaker confirmed (PDF) traces of unauthorized access that led to the exposure of employee and business partner data. The company stated that there is no evidence of customer data being affected.
According to the automotive giant, back in mid December 2025, the company found that data handled through a warehouse management system tied to parts sourced from Thailand had been exposed after unauthorized access.
An internal investigation, carried out with help from an external security firm, confirmed that attackers exploited vulnerabilities in the system and gained access to some of the stored data. The information involved includes 692 records linked to employees and business partners, covering user IDs issued by the company, names, email addresses, company names, and business partner IDs.
Automotive companies have been hit more often in recent months. Last year alone, Renault UK, Jaguar Land Rover (JLR), and Stellantis, which owns brands like Fiat, Jeep, Dodge, Maserati, and Peugeot, all reported data breaches. Jaguar Land Rover is still dealing with the fallout from its incident.
Nevertheless, employees and partners impacted by these data breaches must remain alert as their stolen details, like names, contact information, and job records, can be used later in targeted phishing or impersonation attempts, sometimes long after the initial incident.