A critical vulnerability (CVE-2024-40711) in Veeam Backup & Replication software allows attackers to gain full control without authentication. Immediate updates are essential to protect sensitive data from exploitation.
A critical security vulnerability in Veeam’s Backup & Replication software could allow threat actors to take complete control of affected systems. The vulnerability designated CVE-2024-40711, does not require any authentication, making it particularly dangerous for organizations that rely on Veeam for data protection and backup services.
CVE-2024-40711
CVE-2024-40711 is classified as a critical Remote Code Execution (RCE) vulnerability. It affects Veeam Backup & Replication version 12.1.2.172 and earlier versions. If exploited, this flaw could enable attackers to execute arbitrary code, leading to data breaches and deploying ransomware on vulnerable systems used by businesses worldwide.
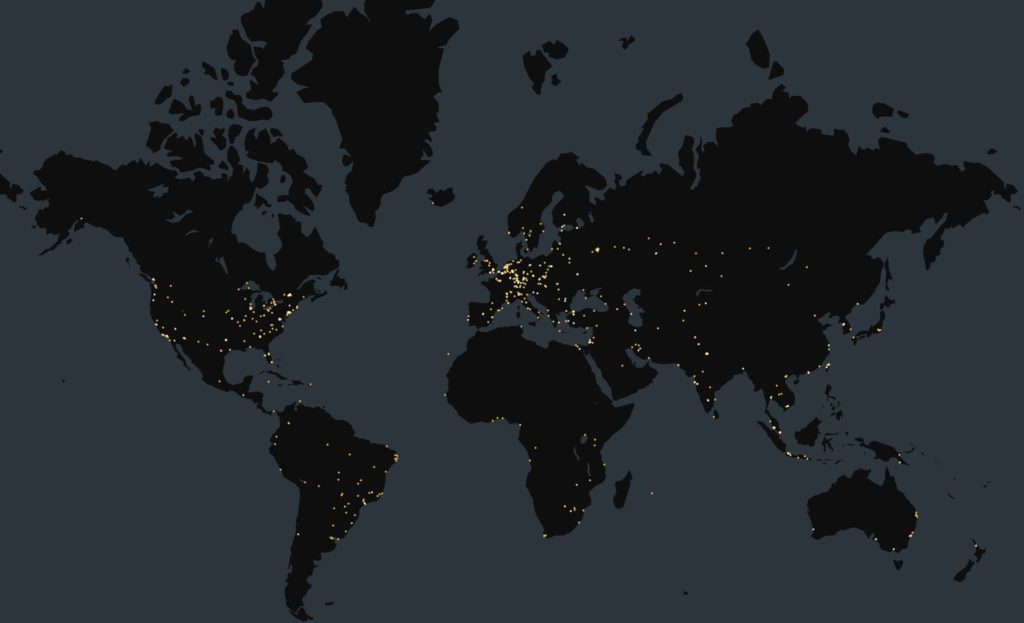
According to Censys, a threat intelligence platform, there are currently 2,833 Veeam Backup & Replication servers exposed on the internet, mostly in Germany and France.
Not the first time
This isn’t the first time Veeam’s software has been vulnerable to such attacks. Earlier this year, another vulnerability (CVE-2023-27532) which was disclosed in July was exploited by notorious ransomware groups like EstateRansomware, Akira and FIN7. The exploitation allowed threat actors to hunt for initial access, credential theft, and other malicious activities.
The increasing trend of ransomware attacks means that CVE-2024-40711 could be exploited similarly, leading to scenarios where organizations might face double extortion, where attackers not only steal data but also threaten to release it unless a ransom is paid.
Veeam’s Response
The good news is that Veeam was quick to release patches for version 12.2.0.334 of their software, which also addresses five other vulnerabilities of lesser severity. All users must update their systems immediately to protect against potential attacks.
Users are urged to upgrade to Veeam Backup & Replication version 12.2.0.334 or later immediately. Organizations should also review their network security protocols to ensure that backup servers are not unnecessarily exposed to the internet. Additionally, regular monitoring and auditing for unauthorized access or unusual activities on the network is essential for maintaining security.