Bluesky, the widely used alternative to Twitter/X, is back to normal after several days of outages that left the platform nearly empty. The issue began on 15 April 2026 at around 11:40 PM PDT, when feeds stopped refreshing. By the next morning, the whole thing had fallen apart as notifications didn’t show up, search was dead, and users couldn’t even open a thread.
According to Bluesky’s official statement, the site was hit by a Distributed Denial-of-Service (DDoS) attack. In this case, hackers flooded the site’s API (Application Programming Interface), which carries information between your phone and the app’s servers, with junk traffic to jam the system, successfully cutting the communication lines for millions.
Bluesky kept it understated while they fought to stay online, telling everyone on X.com– “We are experiencing some service interruptions and our team is working on the issue.”
Who are the Attackers?
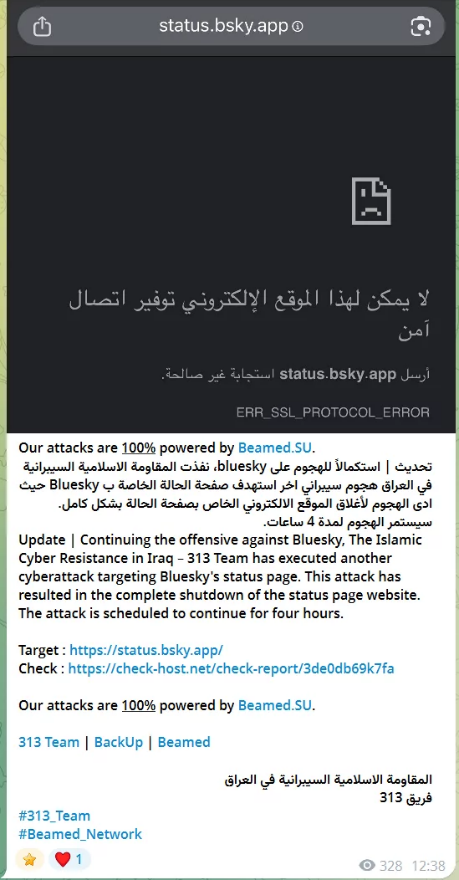
While Bluesky didn’t want to guess who was behind it, a group of hackers calling themselves the 313 Team or the Islamic Cyber Resistance in Iraq started bragging about it on Telegram.
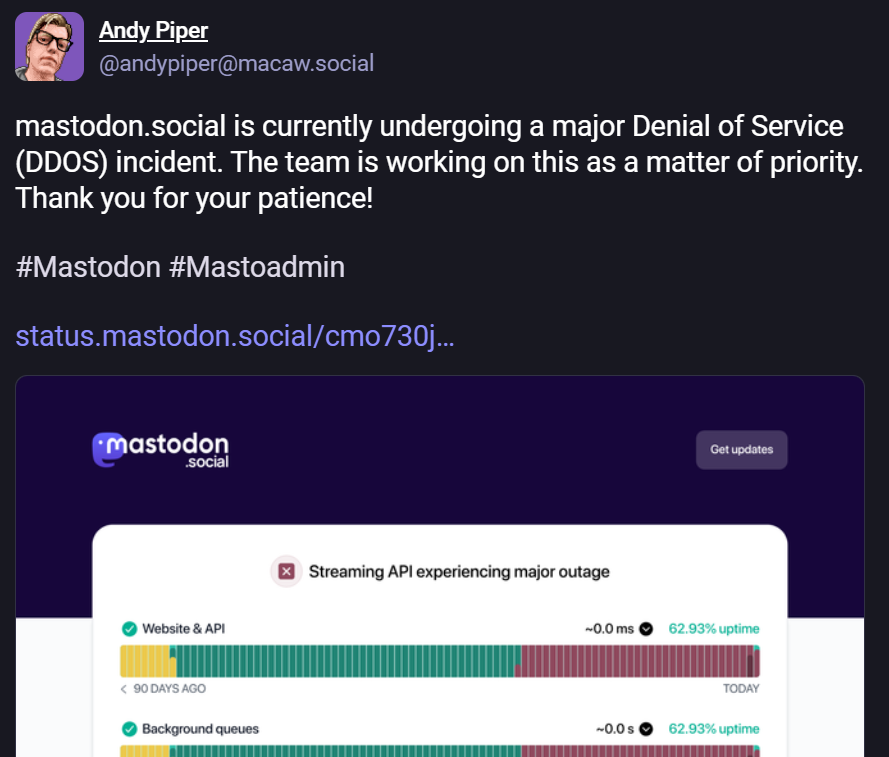
These attackers have links to Iran and a habit of attacking sites they see as being on the side of the US or Israel. Just a few days later, on 20 April 2026, they also went after mastodon.social. However, the site didn’t suffer as much because its servers are spread out.
For context, this group has been very active lately, with its most recent target being Bahrain. Last month, 313 Team launched a similar attack that jammed government websites.
While other groups like Handala usually try to steal data, the 313 Team seems more interested in just causing a scene by shutting things down for a few hours to get attention than spying on users. They like to hop from one social network to another, and mostly just post screenshots of the sites they’ve attacked to show off.
What about your data?
With over 43.7 million users, any cyberattack on Bluesky is likely to raise concerns about the safety of their personal data. But the good news is that because a DDoS attack is just meant to crash the site, not breach into servers, your personal details are safe. Bluesky confirmed this in a post on 18 April, noting that it hasn’t seen “any evidence of unauthorized access to private user data.”
By 20 April, Bluesky sent a final update saying the app was officially stable again.
However, the attackers repeatedly flooded the servers, but the platform’s cybersecurity team contained the attacks and restored normal service, suggesting the worst has passed.