A new Qrator Labs report reveals that the largest DDoS botnet has grown to 13.5 million devices, and hackers can now launch massive 2 Tbps attacks. FinTech and betting industries are the most badly hit in Q1 2026.
A new report from DDoS mitigation provider Qrator Labs shows that DDoS attacks (distributed denial of service attacks) are becoming much larger and more complex. Shared exclusively with Hackread.com, the report, which focused on the first quarter of 2026, reveals that the largest botnet currently tracked by researchers has grown ten times larger in just one year.
This massive network now includes 13.5 million infected devices worldwide, whereas when it was first spotted on 26 March 2025, it only had about 1.33 million devices. These devices are mainly located in the United States (16.0%), Brazil (13.6%), and India (6.5%). Since they are spread across so many different countries, it is much harder for companies to block them based on their location.
Cyberattacker’s Latest Attack Tactics
Qrator Labs report also highlights the growing usage of a relatively new botnet loader (a tool that spreads/controls infected devices) called the Aeternum C2, which uses the Polygon blockchain to send commands to infected computers.
For context, cyber criminals mostly use a central computer to control their attacks, which police can shut down. However, by using the blockchain, there is no central hub to dismantle, making the network hard to stop and reducing the cost for those running it.
Reportedly, multi-vector DDoS attacks also rose from 8.0% to 10.7% of incidents this quarter. Specifically, attacks combining L3-L4 (network and transport layers) and L7 (application layer) methods increased from 3.6% to 6.2%.
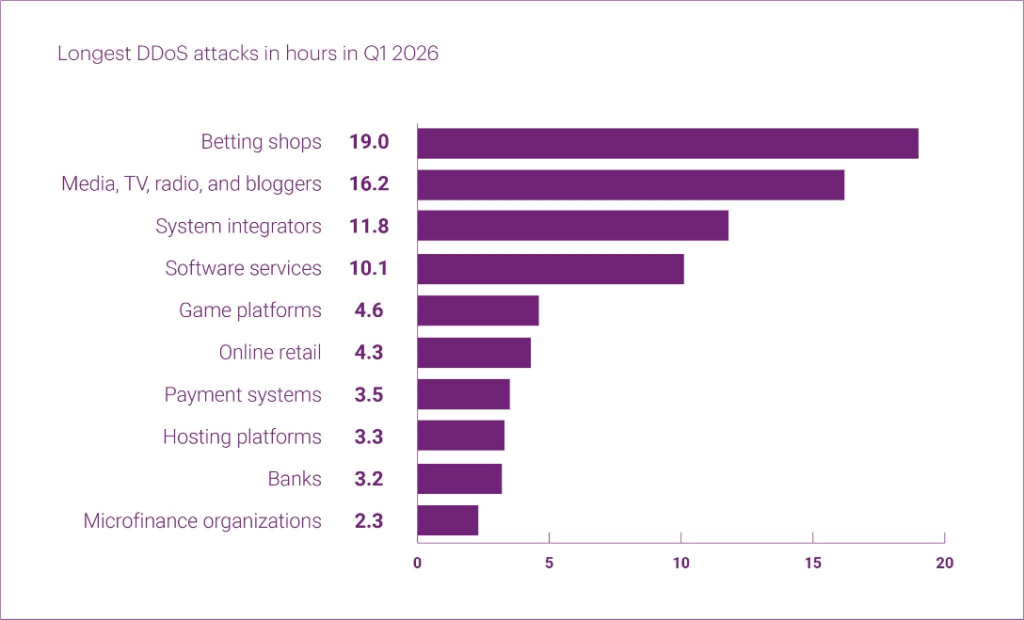
A massive DDoS attack against a company in the betting industry was also detected in mid-March 2026, which reached a peak of 2.065 Tbps and sent nearly 1 billion packets of data every second. These hits usually only last a few seconds at full power, but this one peaked for a stunning 40 minutes. Researchers observed that the hackers tried to change their strategy 11 times during this period to keep the pressure on.
Who is Being Targeted?
Latest data from Qrator Labs shows that threat actors are mostly focusing on money-related businesses. The FinTech segment was hit the most, making up 44.2% of all incidents, with Banks (22.8%) and Payment systems (15.9%) being the main targets. Other common targets included information technology companies (19.3%) and betting shops (10.0%). These areas collectively accounted for nearly three-quarters of all recorded attacks.
Researchers also tracked bad bots. These are automated programmes mainly used for data scraping or hijacking accounts. In the first quarter of 2026, the average number of blocked bad bot requests reached 2.5 billion per month, a 12% increase over the previous year. One attack on a shopping website lasted for over two weeks, with over 178 million malicious requests blocked.
“Traditional defences are less effective” when attackers can use IP addresses from almost any country, the report concludes. With more attacks now using multiple methods like UDP floods and HTTP-based hits at once, the findings show that staying safe online is becoming a much bigger challenge for everyone.