Researchers at exposure management services provider Cyderes have discovered a clever new multi-stage malware campaign that successfully bypasses antivirus software to drain data from unsuspecting users. The firm’s research, shared with Hackread.com, reveals that the campaign relies on two brand-new malware families named Direct-Sys Loader and CGrabber Stealer.
Malware Delivery via GitHub
Cyderes’ unit of elite cybersecurity researchers, Howler Cell Threat Research Team, found that the attack begins with ZIP archives distributed through GitHub user attachment links. One recurring filename discovered was Eclipsyn.zip.
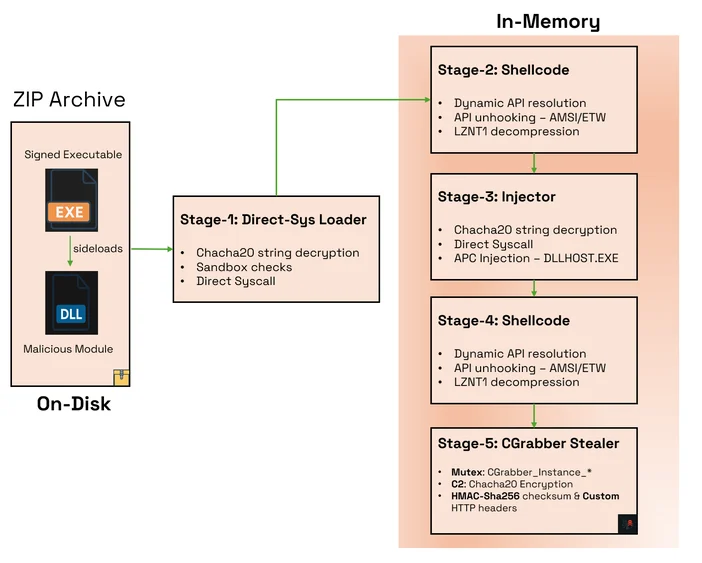
These archives contain a legitimate, Microsoft-signed program called Launcher_x64.exe. This trusted file is tricked into running a malicious component through DLL sideloading, and the component is disguised as a dependency named msys-crypto-3.dll. In the next phase of the attack, the Direct-Sys Loader begins its work.
The blog post reveals that this loader runs a series of checks to see if it is being monitored before doing anything. It then searches for 67 different security tools and also checks for virtual environments like VMware, Hyper-V, or VirtualBox.
If the loader detects a researcher’s sandbox, it simply quits. As per researchers, the malware uses direct syscalls to communicate directly with the operating system kernel. This helps it remain undetected because it silently bypasses the usual security hooks that monitor for suspicious activity, making it a very effective tool for silent intrusion.
CGrabber Data Theft
After the loader confirms the system is undefended, it executes the final payload known as the CGrabber Stealer, which is responsible for stealing the data. And, it does a fairly good job by grabbing an enormous range of personal information across dozens of apps.
CGrabber, reportedly, steals saved passwords, credit card info, and cookies from browsers like Chrome, Edge, Brave, and Firefox, and also targets private keys from over 150 crypto apps, including MetaMask, Exodus, Coinbase, and Binance.
Even communication tools are not spared as the stealer obtains data from Telegram, Discord, Steam, and VPN services like NordVPN and ProtonVPN. Additionally, the stealer performs a CIS check (regional location check), and if the device is located in a country within the Commonwealth of Independent States, it immediately shuts down. Researchers noted that this is a common tactic threat actors use to avoid alerting law enforcement in those specific regions.
Advanced Evasion
The level of discipline shown in this campaign is incredibly high, given that all stolen data is encrypted using the ChaCha20 algorithm before sending it to their servers. Because the malware uses custom web headers like X-Auth-Token, it can easily pass through network filters.
This research into the new threat was shared exclusively with Hackread.com. The best way to stay safe is to be wary of any ZIP file from GitHub and to monitor your system for strange files appearing in folders you didn’t create.