We’ve all done it- clicked a box to prove we’re not a robot without thinking twice. But according to the latest research from Netskope Threat Labs, that split-second habit is exactly what scammers are banking on.
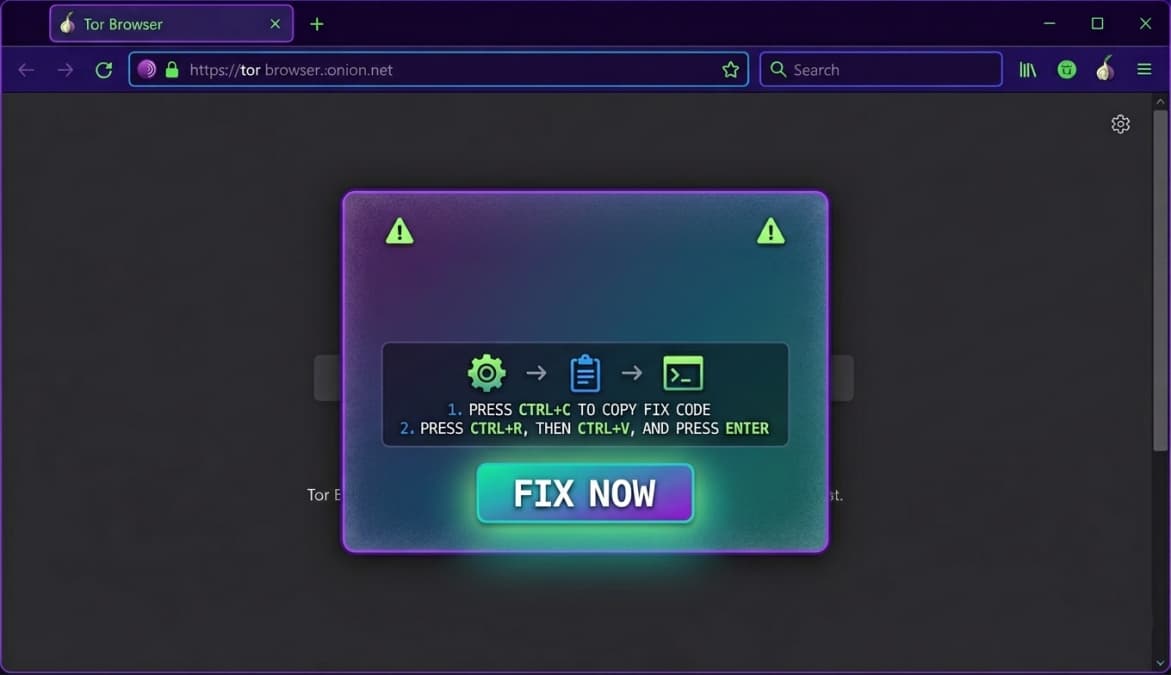
This operation, known as a ClickFix attack campaign, has been spreading rapidly since early 2025. While ClickFix refers to the deceptive technique used to trick you, this campaign is a professional setup specifically designed to drain cryptocurrency from Windows users.
How the Trap is Set
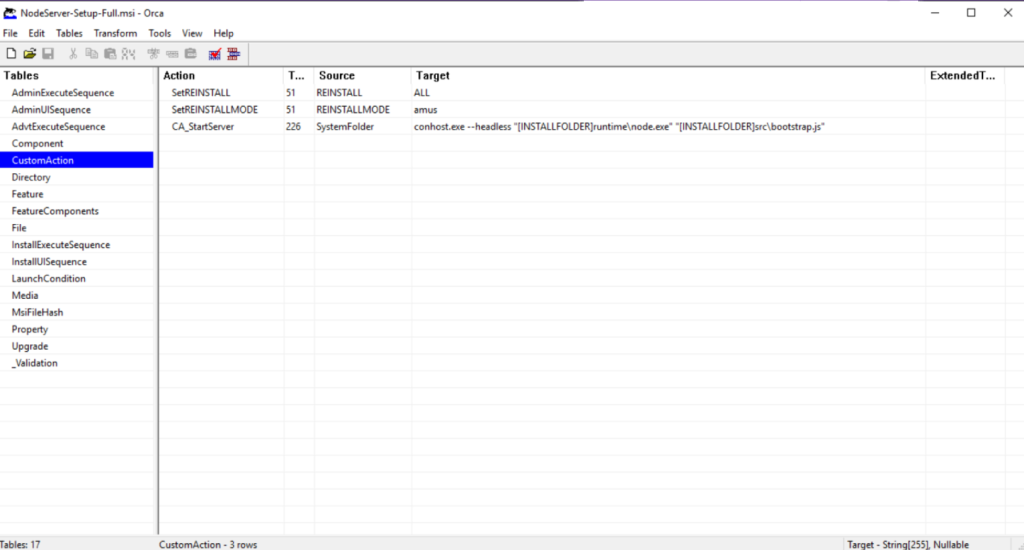
It starts with a fake CAPTCHA. When you click, you aren’t verifying anything; instead, a hidden PowerShell command triggers in the background. It happens so fast that most victims have no idea their machine just reached out to cloud-verificatecom to grab a file called NodeServer-Setup-Full.msi.
This isn’t just a simple virus; it’s a Remote Access Trojan (RAT). It works so well because it includes its own Node.js runtime, a built-in engine that lets the malware run on any Windows PC without needing other software. To stay hidden, it immediately uses the Tor network to mask its traffic, installs itself into a folder called LogicOptimizer, and digs into the Windows Registry to ensure it launches every time you turn on your computer.
A Ghost in the Memory
What’s really worrying is how this software hides. Built on a NodeJS framework, it is modular, which means the most dangerous parts of the code never actually touch your hard drive because attackers steal modules dynamically from their server only when they are ready to strike. These stay in the computer’s temporary memory, making them nearly invisible to standard scans.
Before it starts stealing, the malware performs a ‘fingerprint’ check to scan your system. It checks your Windows version, CPU type, and available RAM. It even looks for over 30 security products, including Windows Defender, Kaspersky, Norton, and McAfee. If the computer looks too well-protected, the malware stays quiet to avoid detection.
“This architecture confirms the malware is both an infostealer and a RAT, the C2 capabilities documented in support.proto can execute arbitrary code, manipulate files, and run system commands,” the blog post reads.
The Crime Factory Exposed
Researchers noted that this isn’t the work of a lone hacker but a Malware-as-a-Service (MaaS) operation, which is a professional business in which scammers rent a toolkit to launch their own attacks.
The Netskope team caught a massive break when the attackers made an OPSEC failure, leaving their admin panel exposed. Recovered files like support.proto and admin.proto provided researchers with a structural map of the backend, revealing that the hackers use a protocol called gRPC to communicate with the infected computer in real-time.
This allows the affiliate groups, the individual scammers who rent this technology, to use Tor-based communication to instantly track cryptocurrency wallets and send success alerts to their own Telegram channels.
Nevertheless, these scammers are professional and experts at staying anonymous. Therefore, as a precautionary measure, if a verification box feels even slightly off, close the tab to protect your crypto wallet.