New Linux malware ‘Perfctl’ is targeting millions worldwide, mimicking system files to evade detection. This sophisticated malware compromises Linux servers, exploiting vulnerabilities for cryptomining and system resource hijacking.
Cybersecurity researchers at Aqua Nautilus have discovered a new Linux malware that has targeted millions worldwide, exploiting over 20,000 misconfigurations. The malware has been lurking for some time, but recently attacked a Nautilus honeypot, providing an opportunity to detect and examine this threat that can put any Linux server at risk.
According to Aqua Nautilus, this sophisticated Linux malware dubbed “perfctl” has been quietly targeting servers worldwide over the past few years. This highly persistent and evasive threat has been actively seeking vulnerabilities and misconfigurations to compromise systems.
The malware’s name comes from the cryptominer process, which drains system resources and causes significant issues for Linux developers. In the company’s technical research, shared exclusively with Hackread.com ahead of publishing on October 3 Thursday, there have been numerous incident reports and discussions in online communities pointing to the widespread prevalence of perfctl.
The malware’s impact has been felt across various developer forums, including Reddit, Stack Overflow, and others. “Usually in some of these posts, you can find replies with links to reports about the malware written by researchers. But in this case, however, none of these had links to such reports,” noted Assaf Morag and Idan Revivo in their research.
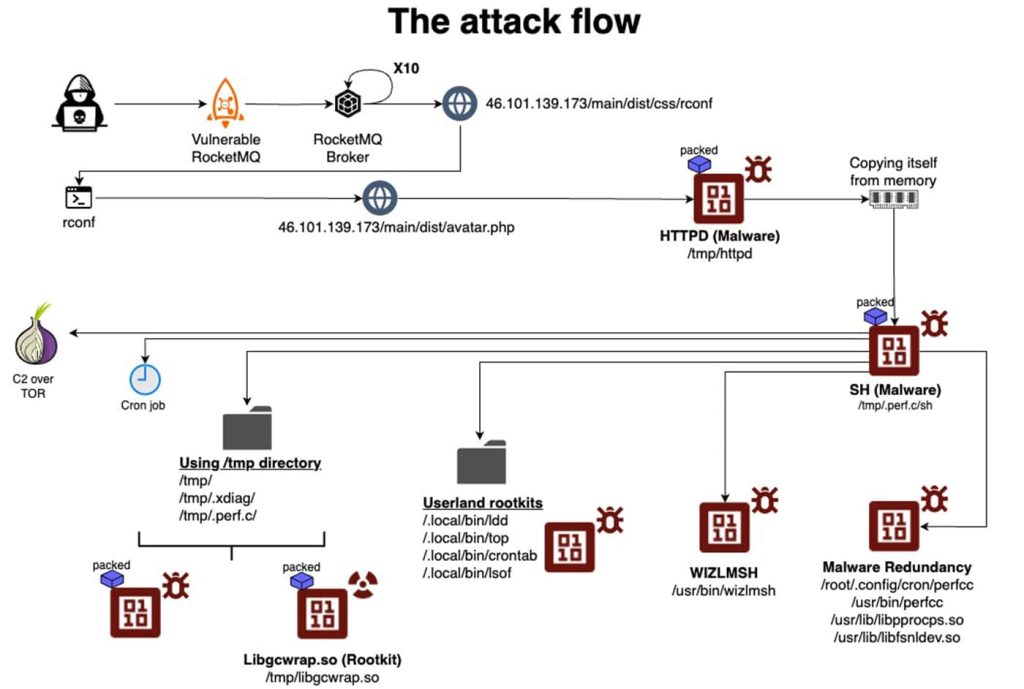
Another concerning trend highlighted by researchers is that Perfctl uses rootkits and evasion techniques to hide its presence from standard system tools and monitoring processes. It temporarily suspends its activities when new users log in, making it harder to detect. In addition, Perfctl uses Unix sockets for internal communication and the Tor network for external connections, making it difficult to track its activities.
The attack starts with the malware downloading a main payload from an attacker-controlled HTTP server controlled, named “httpd”. This payload has multiple layers of execution, ensuring persistence and evading detection. The malware copies itself to a new location, runs a new binary, terminates the original process, and deletes the initial binary.
It then executes the main payload under a different name, choosing the process’s name to appear less suspicious. The malware is executed by ‘sh’, changing its name from httpd to sh.
This malware gains persistence by self-replicating and using deceptive filenames that resemble legitimate system files. Perfctl copies itself to multiple locations on the disk, ensuring its survival even after system restarts or cleanups.
Perfctl’s primary goal is cryptomining, using infected systems for cryptocurrency generation. It has also been observed engaging in proxy-jacking, and hijacking server resources for malicious purposes. Perfctl attempts to exploit the Polkit vulnerability (CVE-2021-4043) to gain root privileges, granting it greater access and control over the system.
“Given the scale, we strongly believe the attackers targeted millions worldwide with a potential number of victims of thousands, it appears that with this malware any Linux server could be at risk.”
Aqua Nautilus
Perfctl’s rootkit and evasion techniques make detection challenging, while its deceptive filenames and behaviour can make it appear legitimate. Its dynamic behaviour can also hinder detection efforts.
To protect your Linux systems from Perfctl, regularly update your operating system and software with the latest security patches, conduct vulnerability assessments, implement robust network security measures like firewalls and intrusion detection systems, monitor system activity for unusual behaviour, and use security tools like endpoint protection solutions.