North Korean hackers from Lazarus Group exploited a zero-day vulnerability in Google Chrome to target cryptocurrency investors with a deceptive and fake NFT game. The attackers use social engineering and malicious software to steal sensitive data and potentially deploy further malware.
The infamous North Korean hacking group, Lazarus Group, has launched a sophisticated attack campaign targeting cryptocurrency investors. This campaign, uncovered by Kaspersky researchers, involves a multi-layered attack chain that leverages social engineering, a fake game website, and a zero-day exploit in Google Chrome.
According to the report, Kaspersky Total Security discovered a new attack chain in May 2024 targeting an unnamed Russian national’s personal computer using the Manuscrypt backdoor.
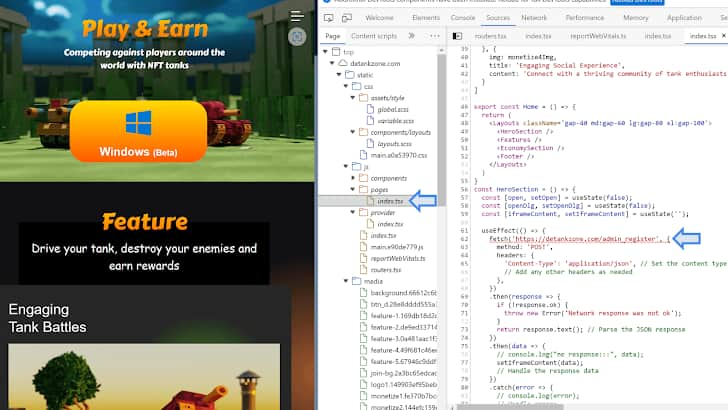
Kaspersky researchers Boris Larin and Vasily Berdnikov estimate that the campaign started in February 2024. Delving deeper into the attack researchers found that the attackers have created a website called “detankzonecom” that appears to be a legitimate platform for a “DeFiTankZone” game.
This game supposedly combines Decentralized Finance (DeFi) elements with Non-Fungible Tokens (NFTs) within a Multiplayer Online Battle Arena (MOBA) setting. The website even features a downloadable trial version, further enhancing the illusion of legitimacy. However, beneath the surface lies a malicious trap.
“Under the hood, this website had a hidden script that ran in the user’s Google Chrome browser, launching a zero-day exploit and giving the attackers complete control over the victim’s PC,” researchers wrote.
The exploit contains code for two vulnerabilities: one allowing attackers to access the entire address space of the Chrome process from JavaScript (CVE-2024-4947) and the second allows bypassing the V8 sandbox to access memory outside the bounds of the register array. Google patched CVE-2024-4947, a type confusion bug in the V8 JavaScript and WebAssembly engine, in March 2024, but it’s unclear if the attackers discovered it earlier and weaponized it as a zero-day or exploited it as an N-day vulnerability.
An n-day vulnerability refers to a security flaw or weakness that has already been discovered, publicly disclosed, and typically patched or mitigated by the software vendor. The term “n-day” indicates that the vulnerability has been known for “n” days, where n represents the number of days since the vulnerability was first disclosed or patched.
Following successful exploitation, the attackers deploy a custom script (validator) to gather system information and determine if the infected device holds any valuable assets worth further exploitation. The specific payload delivered after this stage remains unknown.
In this campaign, Lazarus has targeted influential figures in the cryptocurrency space, leveraging social media platforms like X (formerly Twitter) and LinkedIn. They established a social media presence with multiple accounts on X, actively promoting the fake game, and employed generative AI and graphic designers to create high-quality promotional content for the DeTankZone game. Additionally, the group sent specially crafted emails to individuals of interest, posing as blockchain companies or game developers seeking investment opportunities.
The DeTankZone website itself appears to be built upon the stolen source code of a legitimate blockchain game called DeFiTankLand (DFTL). This game experienced a security breach in March 2024, leading to the theft of $20,000 worth of cryptocurrency.
While the developers suspected an insider, Kaspersky researchers believe Lazarus Group might be responsible for both the theft and the repurposing of the stolen source code for their malicious campaign.
This campaign highlights the evolving tactics of the Lazarus Group. It’s crucial to be wary of unsolicited investment opportunities, especially those involving downloadable game clients or suspicious social media promotions. Additionally, keeping browser software like Chrome updated with the latest security patches is essential to mitigate the risk of zero-day exploits.