The new PG_MEM malware targets PostgreSQL databases, exploiting weak passwords to deliver payloads and mine cryptocurrency. Researchers warn that 800,000 publicly accessible instances are vulnerable. Learn how this multi-stage attack works and how to protect your PostgreSQL environment.
Aqua Security’s threat research team, Nautilus, has discovered PG_MEM, a new malware that can infiltrate PostgreSQL databases, deliver payloads, and mine cryptocurrency.
PostgreSQL, also known as Postgres, is an open-source relational database management system researchers observed as susceptible to brute force attacks. These attacks exploit weak passwords resulting from misconfiguration or insufficient identity controls, a common issue in large organizations.
This, according to the company’s blog post, allows them to gain access to the database and execute arbitrary shell commands by leveraging the COPY … FROM PROGRAM command, leading to malicious activities like data theft or malware deployment.
Nautilus researchers identified 800,000 publicly accessible instances of PostgreSQL databases as vulnerable to this malware. The ultimate goal of the attack is to deploy cryptocurrency miners to exploit system resources.
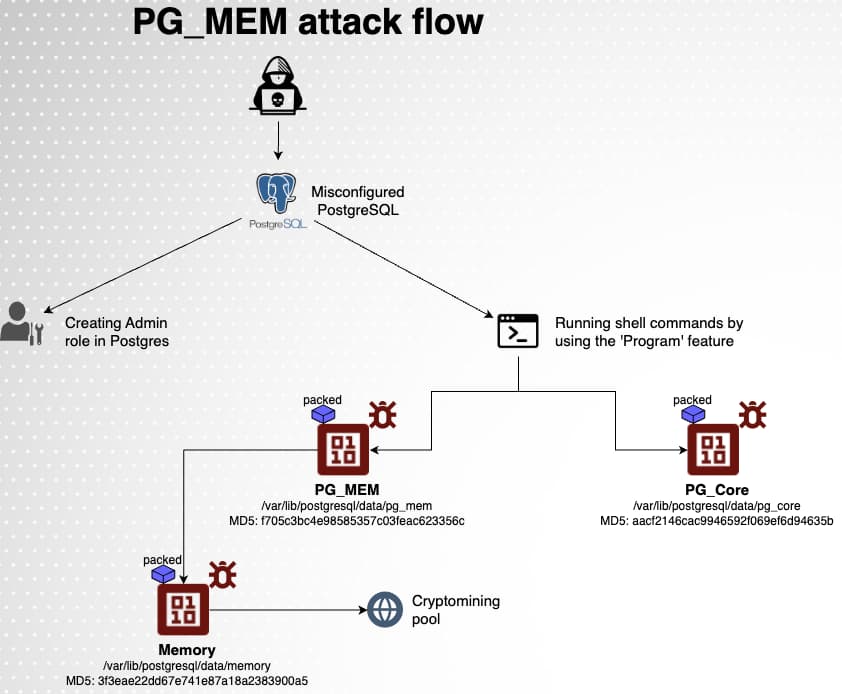
The PG_MEM malware employs a multi-stage attack flow to compromise PostgreSQL databases and deploy cryptocurrency miners. It starts with the attacker initiating a brute force attack on the PostgreSQL database, repeatedly attempting to guess the database credentials. Once this gets done, attackers create a new superuser role with high privileges. This allows them to maintain access to the database even if the original credentials are changed.
Now, the attacker gathers information about the system, such as the PostgreSQL server version and configuration to identify potential vulnerabilities and tailor the attack accordingly. The attacker downloads malicious payloads from a remote server, which typically includes cryptocurrency mining software and tools for persistence and evasion.
Researchers noted that two files are downloaded from the attacker’s remote server, with the first block of commands aimed at delivering the first payload. They used a temporary table to store code and data, clearing it before and after each command. As soon as the payloads are downloaded on the compromised system, the cryptocurrency mining software begins to consume system resources to mine cryptocurrency.
The attacker takes steps to ensure persistence, such as creating cron jobs or modifying system configuration files, which helps the malware to continue operating even after the system is restarted. Moreover, they evade detection by deleting files and logs related to their malicious activity.
This is concerning as PostgreSQL databases are commonly used for web, mobile, geospatial, and analytics applications. To protect PostgreSQL environments, organizations should monitor for suspicious activity, implement strong authentication using robust passwords and multi-factor authentication, isolate databases from the network, and use security tools to promptly detect and prevent malicious activity.