Maintaining user context across distributed applications is a requirement for secure, auditable, and user-focused systems, especially in sectors subject to strict regulations. Without it, teams often encounter missing user attribution in audit logs as requests traverse different systems.
In my experience with banking, healthcare, and technology teams, incomplete user context leads to audit gaps, inconsistent authorization, and failed compliance checks. OAuth 2.0 Token Exchange, defined in RFC 8693, was built to address these issues by supporting delegated access and continuous user context across system boundaries.
This article explains why identity context is often lost, how token exchange fixes it, and what this looks like in practical deployments.
The Modern Enterprise Challenge: What Happens When Apps Lose Context?
In a typical enterprise, it’s common to find dozens of apps, each with its own identity stack. Older platforms may use SAML, while newer cloud apps rely on OAuth or OpenID Connect.
OpenID Connect, as an authentication layer on top of OAuth 2.0, lets apps verify user identity with ID tokens and standard claims. This standardized flow enables applications to maintain user context, supporting secure access and reliable audit trails across distributed environments (OpenID Foundation, 2023).
Despite improvements in protocol design, many workflows still require users to re-authenticate, breaking continuity. IT teams are forced to manage sprawling access tokens, often with inconsistent policies. When services rely on client credentials grants, downstream APIs recognize only the calling application, not the user. This lack of end-to-end user context creates audit gaps and makes regulatory compliance difficult.
OAuth 2.0 Token Exchange: A Modern Solution for a Connected Ecosystem
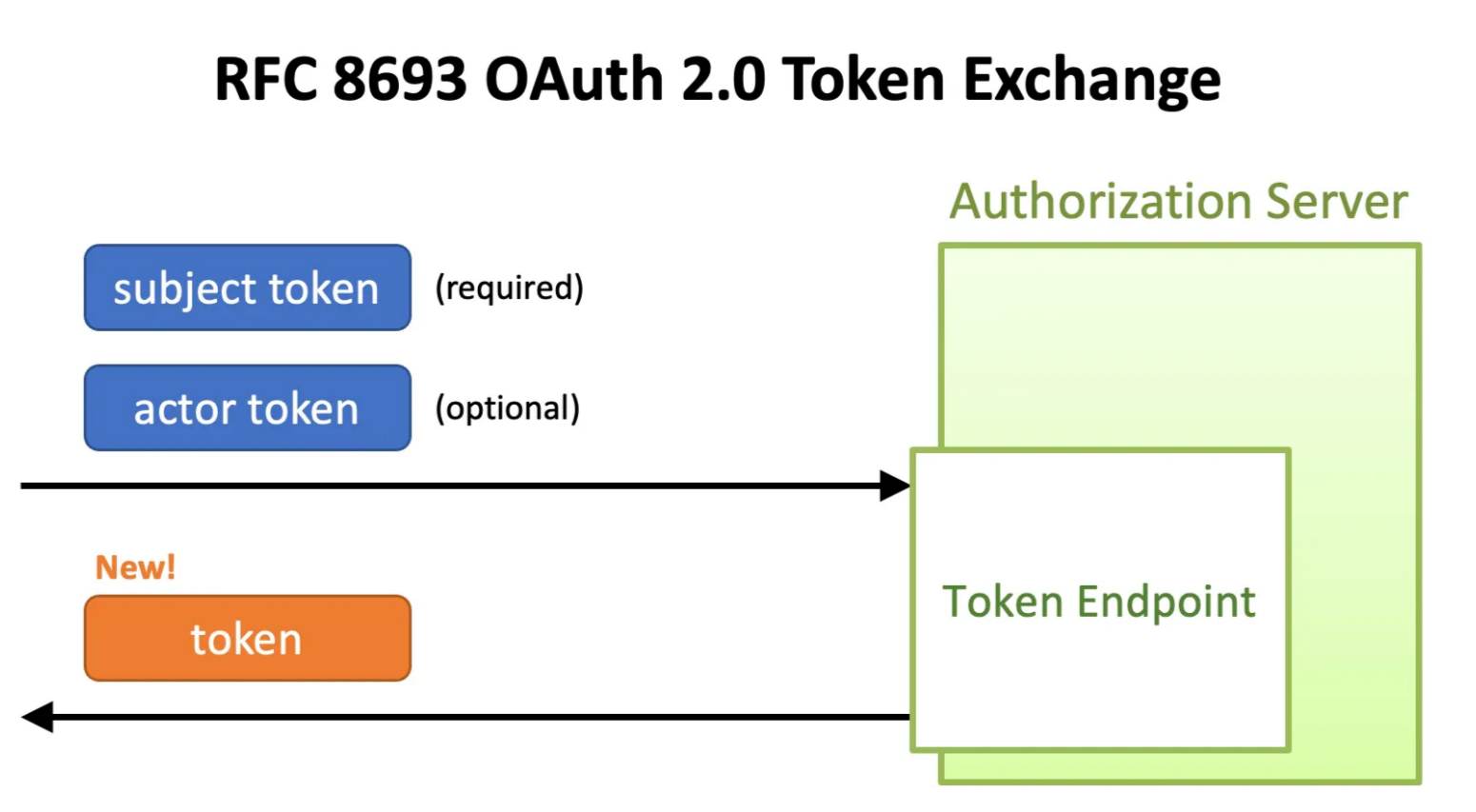
OAuth 2.0 Token Exchange (RFC 8693) extends OAuth 2.0 to support secure, auditable delegation across distributed systems. It allows a service to trade one token for another that’s properly scoped for the downstream API, while carrying forward both user and service identity (Jones et al., 2020).
A token exchange request includes:
- The subject token (the original user’s identity)
- The audience (the intended downstream service)
- Scopes (the specific permissions requested)
RFC 8693 also details how tokens can be used for impersonation (where a service acts as the user) or delegation (where both service and user identities are included in claims).
Token Types and Their Roles in Distributed Authorization
OAuth 2.0 depends on several distinct token types, each serving a critical function in distributed security:
- Access tokens let a client call an API for a limited time and scope.
- ID tokens verify who the user is (especially in OpenID Connect flows).
- Refresh tokens allow longer sessions without repeated logins.
In multi-service chains, a single access token often isn’t enough. Downstream APIs need their own tokens, scoped to their requirements, that retain all necessary claims.
How Token Exchange Works: Step-by-Step Flow
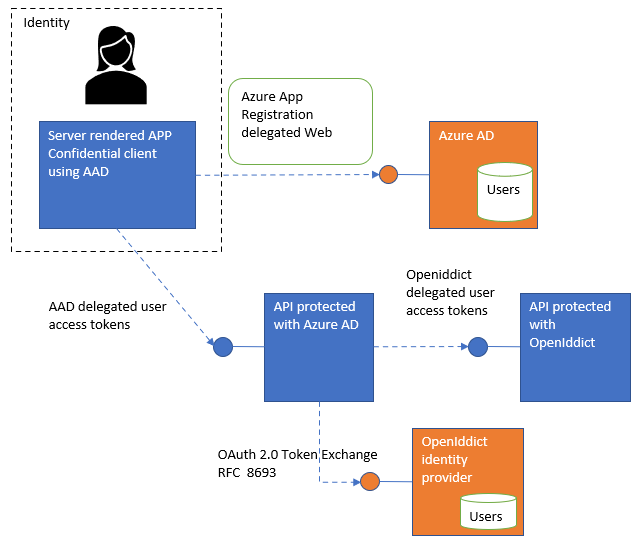
Token exchange allows downstream APIs to retain the original user’s identity throughout a multi-service workflow. This is especially important when services need to access other protected resources on behalf of a user, even across different protocols or authorization servers.
A practical example is a delegated flow between two APIs, one protected by Azure AD and another protected using OpenIddict. The process enables secure delegation and user context continuity between these systems (Damienbod, 2023).
Here’s how the flow works:
1. The user signs in via SSO (OIDC, OAuth, or SAML), receiving an access token.
2. The application uses this token to call API1.
3. API1 submits a token exchange request to the authorization server, providing the original user’s token and specifying the target audience (API2).
4. The authorization server issues a new access token for API2, carrying both the user and the acting service claims.
5. API1 calls API2, which receives and validates the claims, ensuring both user and service are attributable in the audit log.
This process enables every step of the workflow to record exactly who initiated a request and which service executed it, without requiring repeated logins or manual intervention.
How Token Exchange Preserves User Context Across the Enterprise
Traditional SSO and authentication models tend to lose track of the original user as requests traverse backend systems. When service-to-service calls rely on static credentials, identity context disappears, which undermines audit trails and weakens compliance efforts.
Token exchange embeds explicit claims in each token. The sub (subject) claim identifies the original user, while the act (actor) claim records which service is performing the action. The optional may_act claim specifies who is permitted to act as the subject. These claims can be nested to track delegation chains across services (RFC 8693 OAuth 2.0 Token Exchange, 2022).
This is especially valuable in regulated industries, where each action and handoff must be tracked. Organizations gain a consistent method to trace and enforce user intent, even as requests pass through multiple systems.
Enterprise Use Cases: Real-World Scenarios for Secure Integration
Token exchange enables several integration scenarios that are difficult or impossible with legacy SSO or simple client credentials.
SSO Across Heterogeneous Systems
Many organizations use SAML for internal authentication and OAuth 2.0 for cloud services. Token exchange bridges protocols. For instance, a SAML assertion from a corporate IdP can be traded for an OAuth token, preserving user identity as they access SaaS platforms.
Microservices and API Chaining
Modern backend systems often require a user’s request to move through multiple microservices, each needing a token suited to its scope and audience. Token exchange allows each service to obtain a token that represents both the user and its own identity. In healthcare, this supports HIPAA-compliant tracking of which provider accessed patient records, when, and for what purpose.
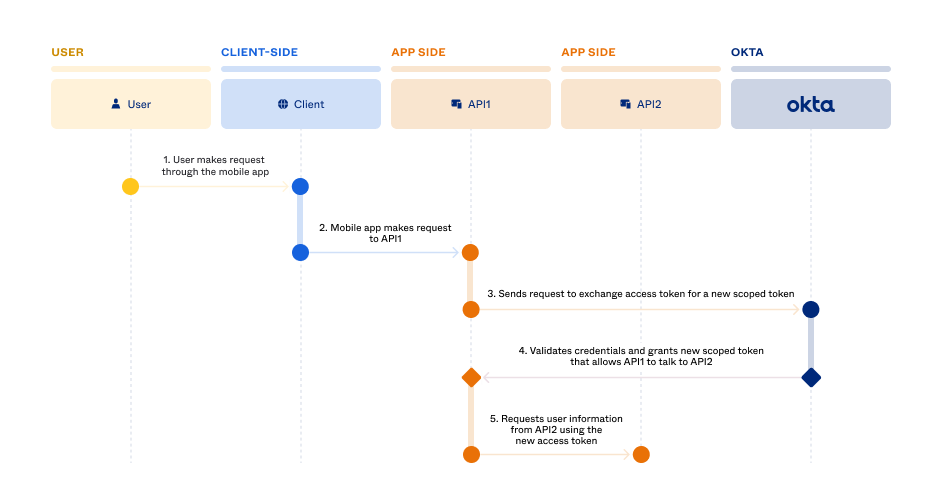
On-Behalf-Of Delegation
Certain workflows require a service to act on a user’s behalf, such as financial transactions or document signing. Token exchange lets the downstream API verify both the user’s identity and the acting service.
Case Study: In Okta’s On-Behalf-of Token Exchange flow, when an initial request is made, the app receives a user-specific access token. If the app must call another API, it exchanges this token for a new one. The new token includes claims for both the original user and the service, allowing every action to be attributed correctly (Okta Developer, 2023).
This process ensures all steps in sensitive operations are fully auditable, which is critical for compliance and fraud monitoring in banking and other regulated industries.
Security and Scalability Considerations
Token exchange strengthens security and simplifies scaling across distributed systems by enforcing key controls at every step. Short-lived access tokens (measured in minutes or hours) limit risk if a token is compromised. Narrow scopes restrict each token’s use to only what is necessary (McGloin & Hunt, 2013).
Audience restrictions are essential. The aud (audience) claim must match the target service, preventing accidental or malicious token reuse. Authorization codes must be single-use. If reused, the system should revoke all related tokens.
Token binding (linking tokens to client identity or device), along with nonces and timestamps, helps ensure each token is valid for only one transaction. All token exchanges and API calls must use TLS to prevent interception and unauthorized use, as OAuth tokens are bearer tokens and can be reused if stolen.
Finally, including both subject and actor in tokens enables precise audit trails. This supports compliance and gives organizations the ability to track who performed each action, even across complex delegation chains.
Token Exchange vs. Traditional SSO and Authorization
Legacy SSO, built on cookies and sessions, cannot synchronize session data across domains or protocols. Token exchange uses stateless bearer tokens that operate across multiple APIs and applications.
Here’s a quick comparison:
| Aspect | Cookie-based SSO | Token Exchange (OAuth 2.0) |
| State Management | Server-side, session cookies | Stateless, bearer tokens |
| Scalability | Challenging across domains | Easily scales across APIs, microservices |
| Context Preservation | Limited in API chaining | Maintained via delegated claims |
| Auditability | Basic (user logs in/out) | Granular (who, what, where, on behalf of) |
| Security | Vulnerable to CSRF, cookie theft | Token lifetimes, scopes, audience binding |
| Protocols Supported | Often tied to legacy (SAML) | OAuth 2.0, OIDC, SAML bridging |
| Performance | Can be session-heavy | Designed for distributed, stateless flows |
For cloud and microservices environments, token exchange is essential for secure, scalable, and auditable integrations.
Conclusion: Making Token Exchange Central to Enterprise Integration
Preserving user context is fundamental to secure, compliant, and efficient enterprise systems. Token exchange gives architects and engineering teams the tools to maintain identity and intent as requests flow between applications and services.
Teams building SSO, microservices, or cross-domain authorization should require token exchange as part of their core identity standards. Audit its implementation regularly to guarantee you’re truly preserving user context, and ensure your organization remains secure and compliant as you scale.
References:
McGloin, M., & Hunt, P. (2013, January 1). OAUTH 2.0 threat model and security Considerations. https://doi.org/10.17487/rfc6819
How OpenID Connect Works. (2023, July 20). OpenID Foundation. https://openid.net/developers/how-connect-works/
Jones, M., Nadalin, A., Bradley, J., & Mortimore, C. (2020, January 1). OAUTH 2.0 Token Exchange. https://doi.org/10.17487/rfc8693
Kawasaki, T. (2022, July 25). RFC 8693 OAUTH 2.0 Token Exchange. Medium. https://darutk.medium.com/token-exchange-b40814d57a15
RFC 8693 OAUTh 2.0 Token Exchange. (2022, July 15). Authlete. https://www.authlete.com/developers/token_exchange/
Bod, D. (2023, January 9). Implement the OAUTH 2.0 Token Exchange delegated flow between an Microsoft Entra ID API and an API protected using OpenIddict. Software Engineering. https://damienbod.com/2023/01/09/implement-the-oauth-2-0-token-exchange-delegated-flow-between-an-azure-ad-api-and-an-api-protected-using-openiddict/
Set up OAUth 2.0 On-Behalf-Of Token Exchange. (2023, February 8). Okta Developer. https://developer.okta.com/docs/guides/set-up-token-exchange/main/