The world’s most famous hacking contest is facing a crisis it didn’t see coming. For the first time in 19 years, Pwn2Own Berlin 2026 has reportedly run out of space. The event, run by Trend Micro’s Zero Day Initiative (ZDI), hit a hard limit on how many hackers it can actually host. For your information, Pwn2Own is a live competition where experts detect zero-day vulnerabilities.
What’s Happening with Pwn2Own Berlin?
This 3-day contest officially starts on 14 May 2026 at OffensiveCon. However, the real action is all happening behind the stage as ZDI staff had to close the event’s registration early on 7 May because they simply couldn’t handle any more entries.
The reason is that the contest has a fixed schedule because every exploit chain must be tested live. This process involves a team of ZDI staff who check the research, set up the exact hardware, and watch the attack happen on stage. And that’s why they can only handle a certain number of attempts. One of the dejected experts, Ryotkak, spent three weeks trying to sign up, only to be told the event was at maximum capacity.
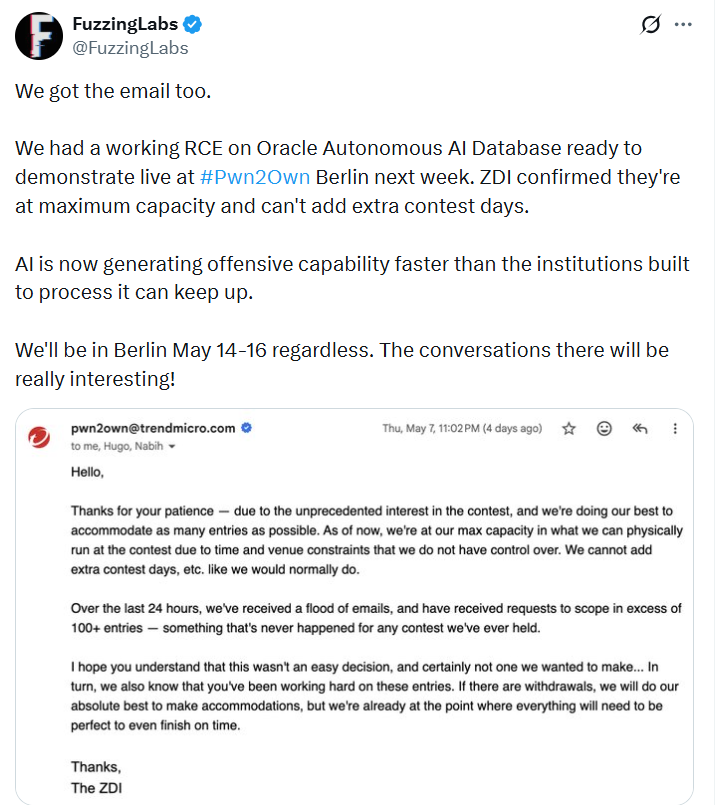
This bottleneck is happening because hackers are finding security flaws faster than the company can process them. Much of this speed comes from new Artificial Intelligence (AI) categories. This year, hackers are targeting tools like Claude Code, GitHub Copilot, Cursor, Ollama, and LM Studio. A report from Palisade Research suggests that AI is now helping these researchers build exploit chains at a speed that traditional contests can’t match.
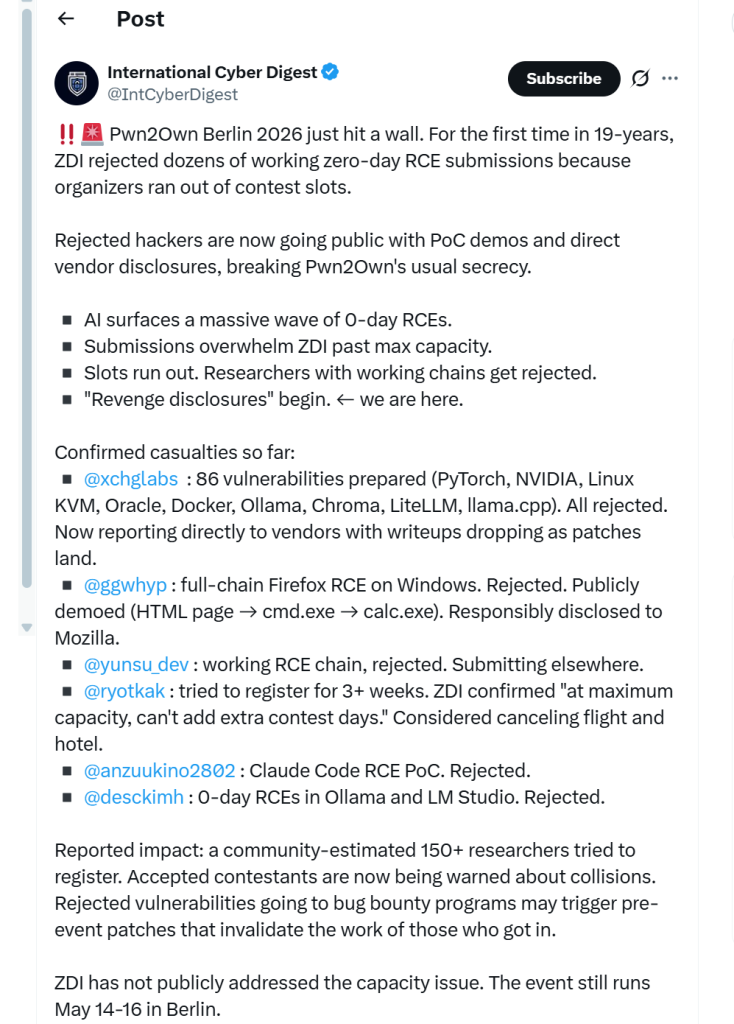
Researchers Go Public with Findings
Because they were rejected, dozens of researchers are now releasing their secrets for free. This is being called a “revenge disclosure” wave. The group xchglabs had 86 vulnerabilities ready for systems like NVIDIA, Docker, Linux KVM, and PyTorch. Since they can’t compete for the $1,000,000 prize pool, they are sending their findings straight to the companies and posting the details online.
Another researcher, ggwhyp, showed off a way to take over Firefox on Windows by making it open a calculator app. FuzzingLabs also had a way to break into an Oracle Autonomous AI Database that will now be shared outside the contest.
This is bad news for the hackers who actually got a spot in Berlin because if a rejected researcher reports a bug today, companies like Mozilla or Anthropic might fix it immediately with a silent patch. If a company fixes the software before the contest starts, the hacker’s work becomes a collision or an n-day, which means it isn’t a secret anymore.
In this case, the effort of those lucky contestants who made it to the stage might already be useless, and unfortunately, they won’t receive any reward. What’s even worse is that the secrecy and hype that usually surrounds Pwn2Own is gone, and the event hasn’t even started yet.