Hackers exploiting a critical Windows flaw (CVE-2022-38028) in the Print Spooler service. Patch immediately to block APT28 (Forest Blizzard and Fancy Bear) attacks & protect your system!
Microsoft issued a security warning about a critical vulnerability (CVE-2022-38028) in the Windows Print Spooler service that attackers are actively exploiting. This vulnerability allows attackers to escalate privileges on a compromised system, potentially granting them complete control.
The vulnerability resides in how the Print Spooler processes JavaScript code. By manipulating a specific file, attackers can execute malicious code with administrator privileges.
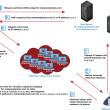
Microsoft attributes these attacks to the APT28 hacking group (also known as Fancy Bear or Forest Blizzard) which is using a custom malware tool called GooseEgg. While the exact timeframe for GooseEgg’s activity is unknown, Microsoft has observed it being operational since at least June 2020.
Microsoft has identified longstanding activity by the Russian-based threat actor we track as Forest Blizzard using a custom tool we call GooseEgg to exploit CVE-2022-38028 in the Windows Print Spooler service to elevate permissions and steal credentials: https://t.co/YKHvxqJa61
— Microsoft Threat Intelligence (@MsftSecIntel) April 22, 2024
Targets of these attacks include organizations in North America, Western Europe, and Ukraine across various sectors such as government, non-governmental organizations (NGOs), education, and transportation.
To mitigate this risk, Microsoft strongly recommends that all users install the security patch they released in October 2022. This patch addresses the vulnerability and prevents attackers from exploiting it.
While Microsoft offers temporary mitigation steps for those who cannot patch immediately, patching remains the most effective way to address this vulnerability and protect your system.
Nevertheless, it’s crucial to consistently update your Windows systems with the latest security patches, as this is the most effective defence against vulnerabilities. Additionally, exercise caution when interacting with attachments or links, particularly in emails from unfamiliar sources, as phishing attempts are a prevalent method used by attackers to compromise systems.
It is also important to know that the Cybersecurity and Infrastructure Security Agency (CISA) has also flagged CVE-2022-38028 as a high-risk vulnerability, given its ongoing exploitation.
RELATED TOPICS
- Microsoft Executives’ Emails Breached by Russia Hackers
- Russian Hackers Target Ubiquiti Routers for Data, Botnet Creation
- Russian Operatives Expose German Military Webex Conversations
- Russian Midnight Blizzard Hackers Breached Microsoft Source Code
- Russian Hackers Hit Mail Servers in Europe for Political, Military Intel