A hacking group linked to Russian military intelligence, identified as Forest Blizzard hackers (aka Fancy Bear), has been caught exploiting thousands of home and small-office routers to conduct a massive surveillance operation.
According to Microsoft Threat Intelligence, which published its findings on April 7, the group has been manipulating these everyday internet devices to intercept private data and monitor network traffic on a global scale.
While this activity has been tracked since at least August 2025, the scale of the operation is becoming clear only now. The research indicates that the group, and a sub-group known as Storm-2754, is using these common gadgets to create a hidden network for international espionage.
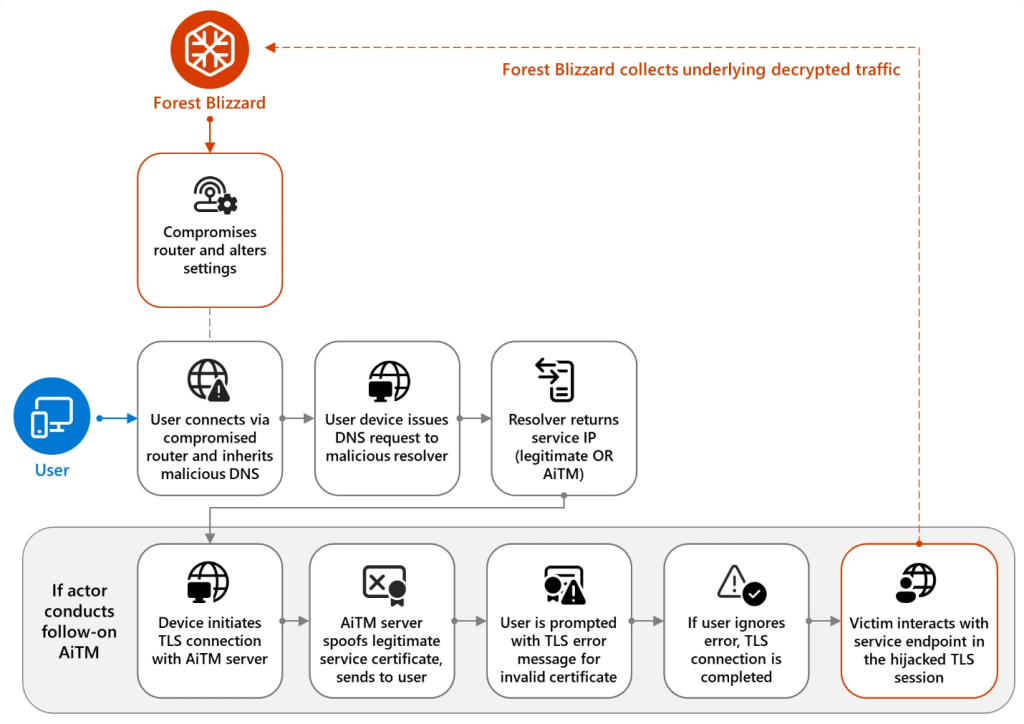
The hackers focus their efforts on Small Office/Home Office (SOHO) devices. These routers are a preferred target because they generally lack the advanced security found in large corporate networks. Researchers noted that the attackers break into these devices to perform DNS hijacking, a technique that reroutes a user’s internet traffic.
The Domain Name System (DNS) acts like the internet’s phonebook, translating website names into the digital addresses computers use to connect, and by taking control of this process, the hackers can secretly direct users to servers they control.
Further investigation revealed the group used a legitimate tool called dnsmasq to manage these redirections, providing them with what researchers described as “persistent, passive visibility and reconnaissance at scale.”
Targeted Attacks on Private Data
The scope of the operation is worrying, with over 5,000 consumer devices and 200 organisations impacted so far. Microsoft researchers noted that the campaign has evolved beyond simple monitoring into Adversary-in-the-Middle (AiTM) attacks in which the hackers position themselves between a user and the service they are trying to reach.
It must be noted that they specifically targeted Microsoft Outlook web users to intercept emails and sensitive content. The energy, IT, and telecommunications sectors have been primary targets, and research reveals the group successfully intercepted data from three government organisations in Africa.
Securing the Remote Workforce
The research highlights a major risk for businesses. Researchers wrote that “compromised home and small-office network infrastructure can expose cloud access and sensitive data,” even when the main office network remains secure. This is particularly concerning for the growing number of people working in hybrid or remote environments.
To mitigate these risks, Microsoft recommends using multi-factor authentication (MFA) and passwordless logins to prevent hackers from using stolen credentials. Furthermore, organisations are encouraged to avoid using basic home routers for corporate tasks and to ensure all devices are kept up to date since the security of an entire network depends on the strength of these individual devices.