Russian hackers launched a targeted malware campaign via Telegram, aimed at Ukrainian military recruits. Disguised as recruitment tools, the malware steals data and spreads disinformation, weakening Ukraine’s defence efforts.
A new report by Google’s Threat Intelligence Group (TAG) exposes a cyber campaign targeting Ukrainian men eligible for military service. The campaign, linked to Russian state-sponsored hackers, orchestrated by the UNC5812 group, utilizes a combination of malware and disinformation.
It is worth noting that at the beginning of October 2024, reports indicated that Russian cyber operations against Ukraine during the first half of the year shifted from broad-spectrum attacks to a more targeted approach, specifically focusing on Ukraine’s military and defence sectors.
For the latest campaign, the immediate objective is to compromise the devices of potential Ukrainian military recruits. Hackers are distributing malicious software to help Ukrainian military recruits locate recruitment centers. These programs are laced with malware that can steal sensitive information like browser data, keystrokes, and cryptocurrency wallet details.
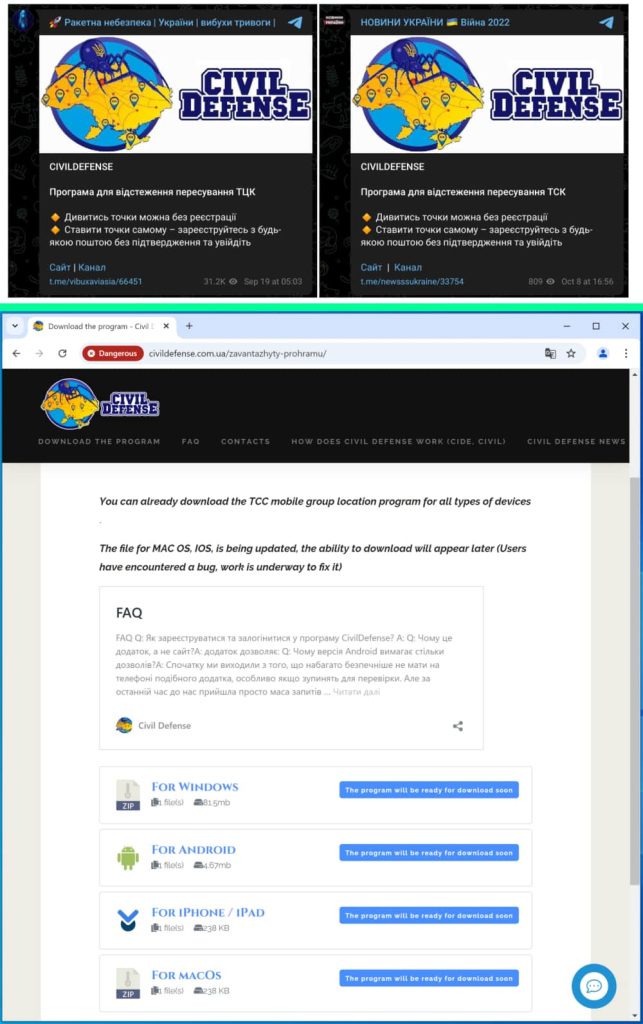
To achieve this, the attackers have established a deceptive online presence through a Telegram channel and website known as “Civil Defense.” Reportedly, the website was registered in April 2024, but the Telegram channel was created in September
These platforms entice users with promises of helpful information and tools related to military conscription. However, once victims download and install the offered software, they unwittingly expose their devices to various malware strains.
For Windows users, this typically involves the Pronsis Loader, which subsequently delivers the information-stealing PURESTEALER. Android users, on the other hand, are targeted with the CRAXSRAT backdoor, a versatile tool capable of data theft, surveillance, and remote control.
To bypass security measures, the attackers have employed social engineering techniques, instructing victims to disable Google Play Protect and manually grant permissions to the malicious apps. The campaign also involves a concerted effort to spread disinformation and undermine public morale in Ukraine.
The “Civil Defense” platform disseminates anti-mobilization narratives, promotes false information about the war, and encourages users to share videos of alleged unfair practices at recruitment centers. The website has a dedicated news section rife with fabricated stories depicting purported injustices surrounding mobilization. The content is posted on pro-Russian social media channels.
The UNC5812 campaign is part of a broader pattern of Russian cyberattacks aimed at destabilizing Ukraine. By targeting potential recruits, the attackers seek to erode public support for the military and hinder Ukraine’s ability to defend itself.
Researchers suspect that UNC5812 is purchasing promoted posts in Ukrainian-language channels to target potential victims. A channel with over 80,000 subscribers promoting the “Civil Defense” Telegram channel-website was observed on September 18th. An additional Ukrainian-language news channel promoting the posts as recently as October 8th suggests the campaign is actively seeking new Ukrainian-language communities for targeted engagement.
Google has identified and blocked malicious websites and domains by adding them to Safe Browsing, actively scanning devices for harmful apps, and collaborating with Ukrainian authorities to block the campaign’s website within the country. Google Play Protect also actively scans devices for harmful apps, including those installed outside the Play Store.
Nevertheless, Google’s report sheds light on Russia’s multifaceted approach to weakening Ukraine’s war effort through cyber means. By staying informed and utilizing security measures provided by platforms like Google, users can help mitigate the impact of such campaigns.
RELATED REPORTS
- Russia Responsible for Widespread Power Outage in Ukraine?
- Ukraine Blocks Russian Industroyer 2 Attack on Energy Provider
- Hackers Claim Data Breach at Russian Cybersecurity Firm Dr.Web
- Russian APT29 Using NSO Group-Style Exploits in Attacks, Google
- Russian Midnight Blizzard Breached UK Home Office via Microsoft









