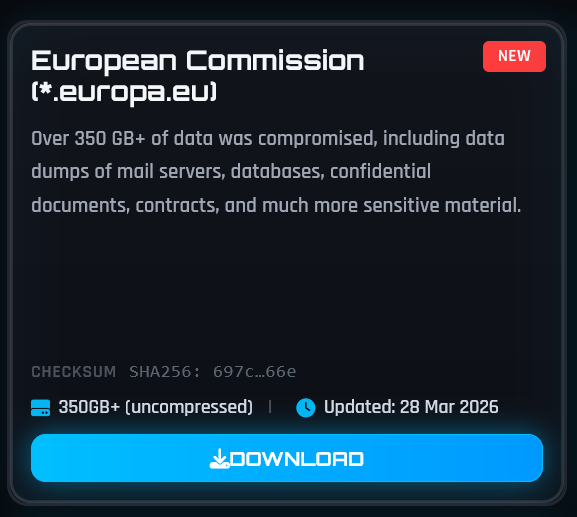
Hackers claiming to be from the ShinyHunters group say they have breached systems linked to the European Commission and released more than 350 GB of data. The claim appeared on the group’s dark web site earlier today, where they also post material linked to earlier incidents involving enterprise platforms.
According to the listing reviewed by Hackread.com, the data is described as a mix of mail server dumps, database exports, internal documents, and contracts. The attackers say the files were obtained through a system compromise, though no technical details have been shared so far to support that claim.
“European Commission (*
ShinyHunters.europa.eu) Over 350 GB+ of data was compromised, including data dumps of mail servers, databases, confidential documents, contracts, and much more sensitive material.”
At this stage, there is no independent verification of the data. The European Commission has acknowledged the reports and said it is investigating. Given the size of the alleged leak, downloading and analysing the full data has not yet been possible, which makes it difficult to confirm both authenticity and impact.
If confirmed, the exposure could involve internal communications and administrative records, which are often as sensitive as personal data in terms of operational risk.
About ShinyHunters
ShinyHunters is a well-known hacking group with a track record of targeting major organisations and selling or releasing stolen data online. The group has been linked to breaches involving companies such as Salesforce partners and other high-profile platforms, often focusing on databases, customer records, and internal systems. Their approach usually involves gaining access to cloud services or poorly secured environments, then extracting large amounts of data for publication or sale.
In the European Commission’s case, reports suggest the hackers accessed its Amazon cloud environment through the Commission’s Amazon Web Services (AWS) accounts. However, an AWS spokesperson has denied any security incident within its cloud environment.
In a related development, the European Commission has issued an official press release confirming that a cyberattack was detected on 24 March, affecting the cloud infrastructure behind its Europa.eu web platform.
The Commission said it moved quickly to contain the incident and keep services running, while early findings indicate that some data may have been taken from the affected websites. At the same time, officials stressed that internal systems were not impacted and that investigations are ongoing to determine the full extent of the exposure.
European Commission and Sensitive Data
It is also worth noting that EU institutions, including the European Commission, do handle sensitive categories of data. This can include biometric information such as facial recognition data, typically used for access control or identity verification within secure systems.
These activities are governed by strict legal frameworks under EU law, with clear limits on how such data is collected and used. However, it remains unclear whether any biometric or identity-related data is part of the alleged leak, and that question will likely be central to ongoing investigations.
Incidents like this show why both public and private sectors, even organisations with strong regulatory oversight and established security practices, can face risks from configuration errors, access control issues, security vulnerabilities, or third-party dependencies.
Nevertheless, this article will be updated based on the European Commission’s outcome of the ongoing investigations. Stay tuned.