Salesforce, a renowned customer relationship management (CRM) platform, has confirmed it is dealing with a significant security incident. The company announced late Wednesday that some of its customers’ data was likely accessed by an outside party through an issue involving apps published by Gainsight, a company that provides customer success software.
“Our investigation indicates this activity may have enabled unauthorised access to certain customers’ Salesforce data through the app’s connection,” Salesforce’s official update stated.
The problem lies with the access tokens used by Gainsight’s connected applications, which are basically special digital keys allowing the apps to link to Salesforce systems. Attackers managed to steal and use these keys to bypass normal security.
Salesforce responded fast, immediately revoking all active tokens for the affected Gainsight apps and removing them from the AppExchange. Access to the Gainsight platform via Salesforce remains unavailable as of this morning. Both companies stressed the issue did not come from a flaw within the core Salesforce platform, but rather through the Gainsight app’s external connection.
The Attack and the Threat
Gainsight’s statement confirms the breach was detected when API calls came from unauthorised (non-whitelisted) IP addresses. As per the company’s update, only three organisations are currently known to be impacted, and Salesforce has proactively reached out to them. The investigation is still ongoing.
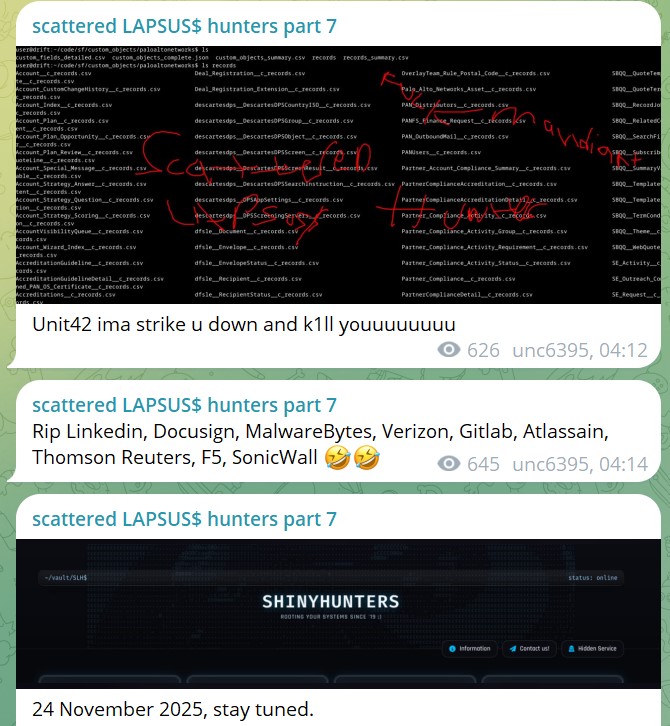
The notorious hacking group ShinyHunters claimed responsibility for the breach, telling DataBreaches.net they used credentials stolen from an earlier attack on Salesloft, where Gainsight was also a victim, to compromise Gainsight.

ShinyHunters claims this combined data theft affects “almost 1000 organisations,” including large companies like the following:
- F5
- Gitlab
- Verizon
- DocuSign
- Atlassian
- SonicWall
- MalwareBytes
- Thomson Reuters
and others from the GainSight campaign.
ShinyHunters claims they used these stolen secrets to gain access to roughly 285 additional Salesforce customer systems. The exposed data potentially includes business contact and licensing details.
Furthermore, the hackers are trying to extort victims, directly threatening Salesforce to create a new data leak site containing data from both the Gainsight and Salesloft campaigns if the platform does not negotiate.
Company Response and Customer Action
Gainsight is working closely with Salesforce and has brought in the top cybersecurity firm, Mandiant, for an independent investigation. Gainsight’s official statement says they will not restore API access until all security layers have been fully reviewed.
Gainsight clarified that any function depending on reading from or writing to Salesforce is affected, including Connector data sync, Rules, Data Designer, Reports, Cockpit, Timeline, and Renewal Center.
However, most in-app workflows using Gainsight-native data are unaffected and run normally. As a precaution, Gainsight also revoked access for its Zendesk connector and temporarily delisted its app from the HubSpot Marketplace.
Customers can request the precise IP ranges for legitimate connections via a support ticket. Gainsight recommends using the direct NXT login method to bypass the Salesforce login block.