Hackers have found a new way to exploit the software world, and this time, they’re using our own trust against us. Researchers at Sonatype have just caught a nasty campaign where legitimate developer accounts were hijacked to spread malicious code. This wasn’t just a random person making a fake app; it looks like a targeted takeover of established creators to inject tampered tools into the system without anyone noticing.
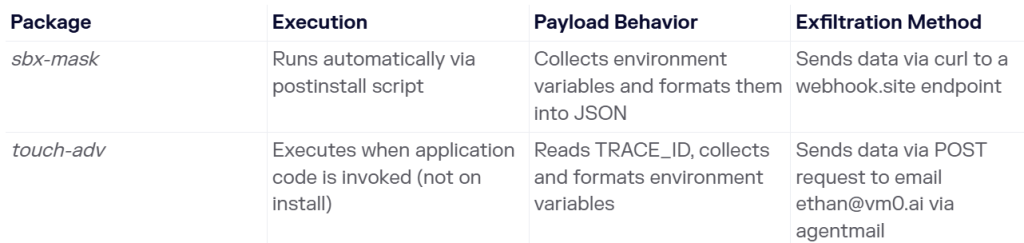
In a report shared with Hackread.com, the firm identified two dangerous packages named sbx-mask and touch-adv. These were quietly published to the npm registry (a massive library of code used by millions) to act as a digital backdoor into a developer’s machine.
Researchers found that these two packages were essentially programmed to act like credential stealers. Once they get onto a computer, they hunt for “environment variables,” which are hidden areas where a computer stores its most private keys, like passwords, API tokens, and login credentials for cloud services.
The two threats, which Sonatype is tracking under the codes Sonatype-2026-001275 and Sonatype-2026-001276, didn’t behave the same way. The sbx-mask package was bold; it triggered its theft the second it was downloaded. On the other hand, touch-adv was more undercover. It stayed quiet until the developer actually started using the software, making it much harder to spot during a quick scan.
Further investigation revealed a very clear trail of where the stolen secrets were being sent. The malware was caught directing data to a specific email address, [email protected], and using a tool called a webhook to move the information out.
As soon as the team realised what was happening, they moved fast and reported it to GitHub’s Security Incident Response Team on March 19, 2026. While the dangerous files have since been kicked off the public platform, they might still be sitting in the private folders of any developer who downloaded them recently.
This shows that avoiding unknown apps might not be enough, even trusted developers can be used to spread malicious code. If you installed these packages, change your passwords and check for unusual network activity right away.