New research from the firm Trellix reveals that hackers are moving toward fileless malware attacks against businesses and organizations. These malware hide in the targeted computer’s temporary memory, allowing them to bypass most standard security software.
The XWorm 7.1 Living off the Land Campaign
As per Trellix’s research, shared with Hackread.com, one of the most dangerous tools identified is XWorm 7.1, a Remote Access Trojan (RAT) offered as malware-as-a-service (MaaS) and gives hackers full control of a victim’s machine.
It is worth noting that XWorm 7.2 is also being sold on marketplaces with the aim of targeting businesses. The availability and capabilities of XWorm have led researchers to label this threat the “commodity king” of the underground, with its use increasing by 174% over the past year.
In a recent campaign targeting a network security firm in Taiwan, hackers used a high-severity flaw in WinRAR (CVE-2025-8088) to get inside. They distributed malicious archives on Discord, disguised as innocent game mods.
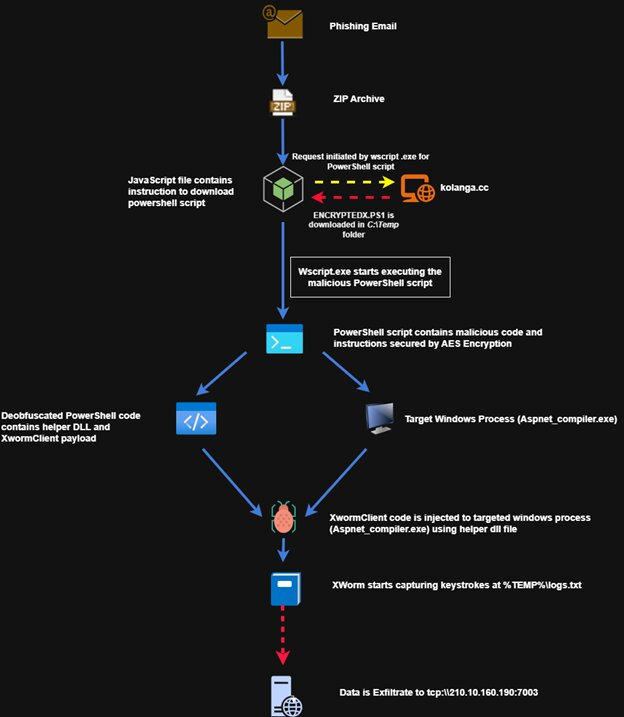
Once a user opened these files, the malware, XWorm, performed a Living off the Land attack by hijacking a trusted Microsoft utility called Aspnet_compiler.exe to run its code. Because the virus stays in the computer’s memory and is never written to the disk, it easily evades older security tools.
“By pivoting from predictable file-based execution to memory-resident, ‘Living off the Land’ (LOTL) techniques, XWorm effectively neutralizes signature-reliant defences… rapid ascent to the #3 global threat ranking necessitates an immediate transition toward a proactive, behavior-based security posture,” the report reads.
Remcos RAT and the Cuckoo Strategy
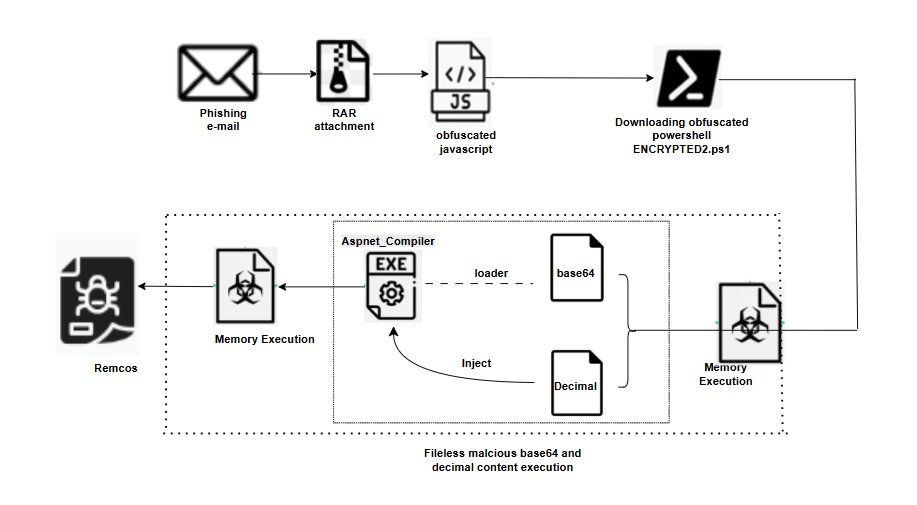
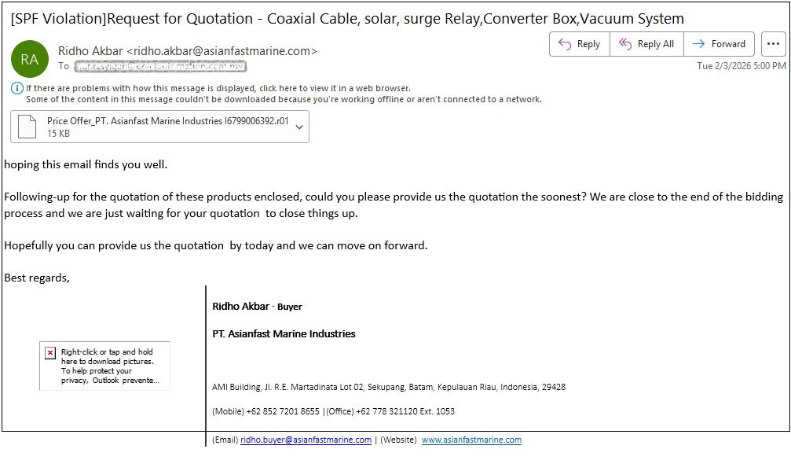
A second report, also shared exclusively with Hackread.com, details a multi-stage attack using the Remcos RAT. This campaign begins with “procurement-themed” emails, such as “request for quotation” lures, to impersonate industrial or marine companies.
If a victim opens the attached ZIP file and clicks the JavaScript inside, it triggers a complex chain of events that leads to process hollowing or the Cuckoo Strategy, which researchers believe is a sneaky move where the malware creates a trusted Windows process and then replaces that process’s insides with the virus.
In this case, it also uses the aspnet_compiler.exe file to hide. Once the Remcos virus is running in the memory, it begins its work of surveillance; it can record every keystroke you type, watch your screen, and even turn on your webcam. The malware even saves this stolen data to a hidden log file in your temporary folder before sending it back to the hacker’s server via a specific connection on Port 7003.
To stay safe, researchers suggest that the best defence is to be proactive with updates. Since these attacks rely on outdated software, it is vital to update WinRAR to version 7.13 or higher immediately. Because hackers are getting better at using our own trusted programs against us, staying alert to suspicious business-like themed emails is more important than ever.
“The campaign reflects modern commodity malware tradecraft, where fileless execution and living-off-the-land techniques are standard, underscoring the importance of memory-centric and behavior-based detection strategies. To harden defenses against these threats, organizations should restrict the misuse of native tools, enforce least‑privilege access, and deploy detection that inspects memory and script execution,” Trellix report concludes.