Cybersecurity team at Endor Labs has identified a critical remote code execution (RCE) vulnerability in protobuf.js, a JavaScript library downloaded nearly 52 million times per week. This research, shared with Hackread.com, highlights a major security gap in an important tool utilised by Google Cloud, Firebase, and various gRPC services, an open-source framework for fast communication between microservices.
The Attack Mechanism
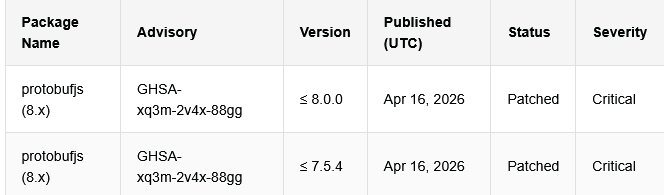
The flaw is tracked as GHSA-xq3m-2v4x-88gg and has a high CVSS score of 9.4. According to Endor Labs’ blog post, the library uses a function called Type.generateConstructor to build JavaScript dynamically.
This process relies on a feature known as the Function constructor, which operates much like an eval() command by turning text into active, running code. In simple terms, the issue is that the library takes names found in a data file and turns them into part of the computer’s working instructions to speed up tasks.
Because the library failed to filter these names, hackers could craft a malicious .proto or JSON file where a “name” is actually a hidden, executable command. By placing a specific string of JavaScript into a type name, a threat actor can force the system to run a payload.
Further investigation revealed that code execution can occur when an application loads and processes a malicious schema, which may happen without direct user interaction in automated or server-side workflows.
Risks to Cloud Infrastructure
The issue can affect applications built on tools such as gRPC or Firebase if they rely on protobuf.js and accept untrusted schema input. Systems that use predefined or trusted schemas are not exposed to this risk.
This includes gRPC reflection services or multi-tenant platforms where users upload their own data definitions. If a hacker influences the schema, they can achieve full RCE and can exfiltrate credentials or move through internal networks.
“This vulnerability is not a supply-chain attack against protobuf.js itself; the package is legitimate and maintained by developers affiliated either now or in the past with Google. It is a vulnerability in how protobuf.js processes the data developers feed it… this class of bugs, dev-tool-as-code-execution-primitive, has an emerging threat model that the ecosystem has been slow to internalize or accept,” researchers explained.
Remediation and Timeline
Researchers found protobufjs versions 8.0.0 and earlier, and 7.5.4 and earlier, being affected by this flaw. They notified the library maintainers about it on 2 March 2026. The vulnerability was confirmed on 9 March 2026, and a fix was reached the npm registry in April 2026. It is a single line of code: jsname = name.replace(/\W/g, ""); that fixes this issue.
This removes the symbols hackers need to run their code. Organisations should audit their systems immediately and update to protobuf.js 8.0.1 or 7.5.5 to close this gap. As researchers concluded that “exploitation is trivial” as soon as a poisoned file is in memory, which makes immediate updates a priority.