Update: This article has been updated with a statement from ASUS confirming the breach.
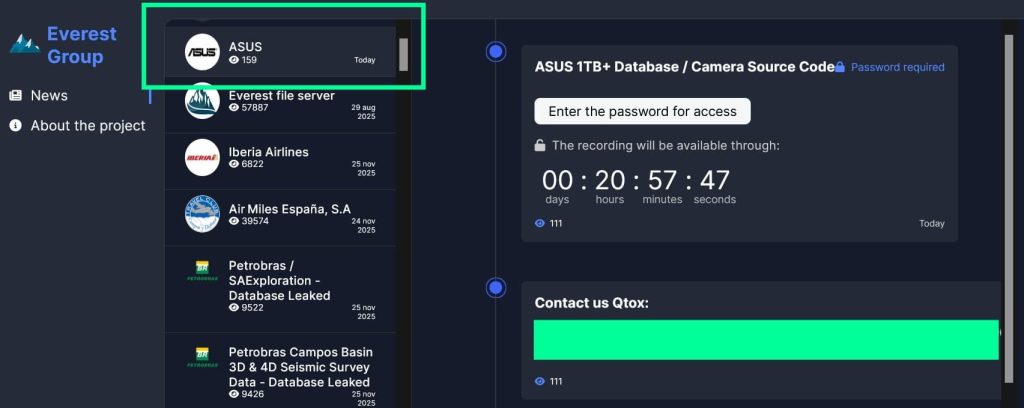
A new claim by the Everest ransomware group suggests that ASUS, one of the world’s largest hardware and electronics companies, has been compromised. According to a post on the group’s dark web leak site, they are in possession of more than 1TB of stolen data, which they say includes camera source code.
In this case, “Camera Source Code” likely refers to proprietary firmware or software used in ASUS devices with built-in cameras, such as laptops or smartphones. This could include low-level control code for camera modules, internal drivers, or even entire applications tied to image processing or device integration.
UPDATE – Type of Allegedly Stolen Data
Claimed Data Leak: Source Code, AI Models, and Internal Tools
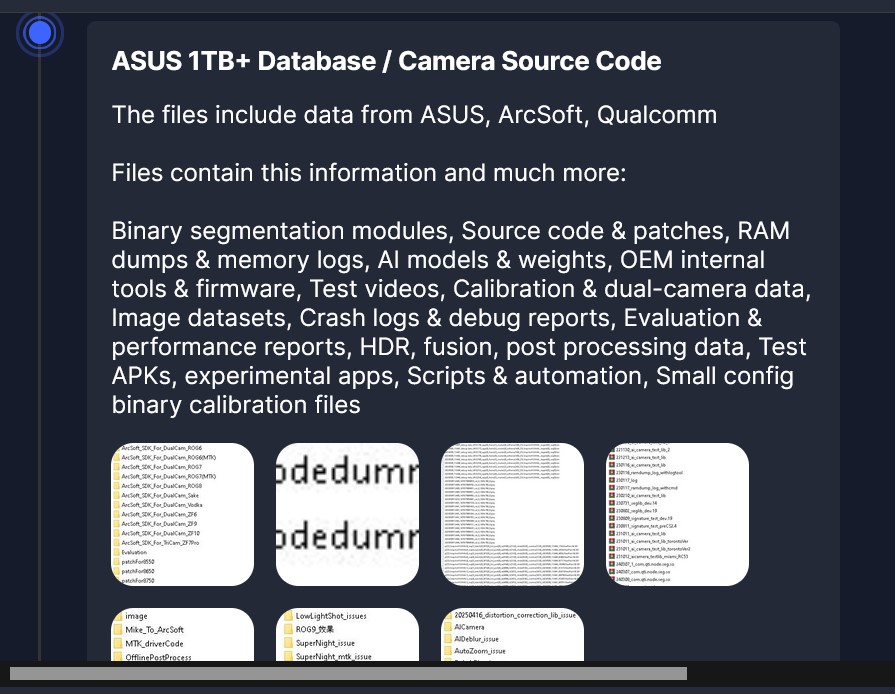
Everest ransomware group has released screenshots as alleged proof of its reported 1TB ASUS breach, exposing highly sensitive internal files not previously disclosed. The leaked material includes complete camera-related source code, internal patches, test modules, and debugging logs.
Folder names indicate SDKs for multiple ASUS ROG phone models, including ROG5, ROG6, ROG7, and ZF series, along with Qualcomm chipset-specific test patches. This points to a breach affecting not just ASUS, but also its partners like ArcSoft and Qualcomm.
AI Models, Memory Dumps, and Calibration Data
The dump includes AI models and their associated weights, raw RAM dumps, segmentation modules, camera tuning configurations, and post-processing scripts. File listings also show .cpp and .h source files for camera modules and image processing libraries.
Additionally, several folders contain specific AI camera testing logs tied to geography-coded builds (e.g., “Toronto,” “Chicago”), along with logs referencing “ArcSoft” and “CDSP,” suggesting proprietary camera software development involving external vendors. Files such as camxchinodedummyrtb.cpp and binary image dumps imply low-level sensor testing, possibly for training or debugging camera AI.
Firmware, Test Apps, and Experimental Builds
The screenshots show a significant portion of internal tools used for camera firmware evaluation and development: test APKs, debug builds, signature testing libraries, and custom automation scripts. There are specific folders for experimental features like Super Night Mode, Bokeh, HDR, and facial recognition (“FD_issue”), along with build logs referencing cinematic video processing.
The presence of configuration binaries, memory logs, and AI segmentation patches suggests that this leak could expose proprietary methods used in ASUS’s mobile imaging pipeline, a serious IP and security risk. Everest claims the data also includes evaluation reports, crash dumps, and app-level prototypes that were likely never intended to leave internal development labs.
Contact Demand
The group is demanding that ASUS contact them through Qtox, an encrypted messaging platform, and has given the company a 21-hour deadline to respond. No ransom amount has been made public, and there’s no clear indication yet of the specific contents or sensitivity of the alleged data.
This claim adds to a series of recent announcements by Everest, which in the past two weeks alone have claimed responsibility for attacks on high-profile organisations, including Under Armour, Brazil’s Petrobras, and Spain’s Iberia airline. Those incidents involved user data, internal documentation, and what the group described as full network access.
ASUS has not yet confirmed or denied the breach. Hackread.com has reached out to the company for comment and will update this story as more details become available.
ASUS, a company known globally for its PCs, motherboards, and consumer electronics, has been targeted before by threat actors. In 2019, the company confirmed that attackers had compromised its Live Update utility in what later became known as ShadowHammer, an attack believed to be state-backed.
If this new claim proves credible, it would be the second significant compromise of ASUS’s infrastructure in recent years. Until there is confirmation or denial from the company, the scope of the incident remains unverified.
UPDATE – ASUS Confirms Data Breach via Supplier Compromise
Following Hackread.com’s exclusive report, ASUS has officially confirmed a data breach affecting its phone camera source code. The breach stemmed from an incident at a third-party supplier, not from within ASUS’s own infrastructure.
ASUS clarified that the breach does not pose a risk to end users, and there is no evidence of compromise to its products or internal systems. The company says it is actively reinforcing its supply chain against future incidents.
“An ASUS supplier was hacked. This affected some of the camera source code for ASUS phones. This incident has not impacted ASUS products, internal company systems, or user privacy. ASUS continues to strengthen supply chain security in compliance with cybersecurity standards,” the company said in a statement.