Update – 20/12/2025: Under Armour has been sued by customers over the Everest ransomware data breach, and Hackread.com’s exclusive coverage has been cited as the primary source in the lawsuit filings. More details on the lawsuit updates are available at the end of this article.
Everest ransomware gang is claiming to have breached Under Armour, Inc., the American sportswear giant, and stolen 343 GB of internal company data, employee information, along with personal data of millions from various countries. The claims were published earlier today on the group’s official dark web leak site.
Sample Data Includes Sensitive Customer and Product Information
As seen by Hackread.com, the group has also published sample data to prove the authenticity of their claims. The sample data contains customer information and their shopping history, along with other details, including email addresses, phone numbers, purchase timestamps, product identifiers, prices, quantities, store preference records, location data for cities and regions, marketing campaign logs, deep link tracking entries, and identifiers tied to user accounts and transactions.
The leaked data also includes detailed product catalogue records linked with customer information, indicating it may originate from a marketing, personalisation, or product registration system. Each entry contains product details such as SKU, name, type, category, size, colour, prices, availability, ratings, localised descriptions, and multiple regional links.
In addition to this, the records expose customer data, including email addresses, first names, consent status, language preference, and request timestamps. This combination of commercial and personal information reveals both product-level business intelligence and individual user behaviour, making it a serious data exposure if verified by Under Armour.
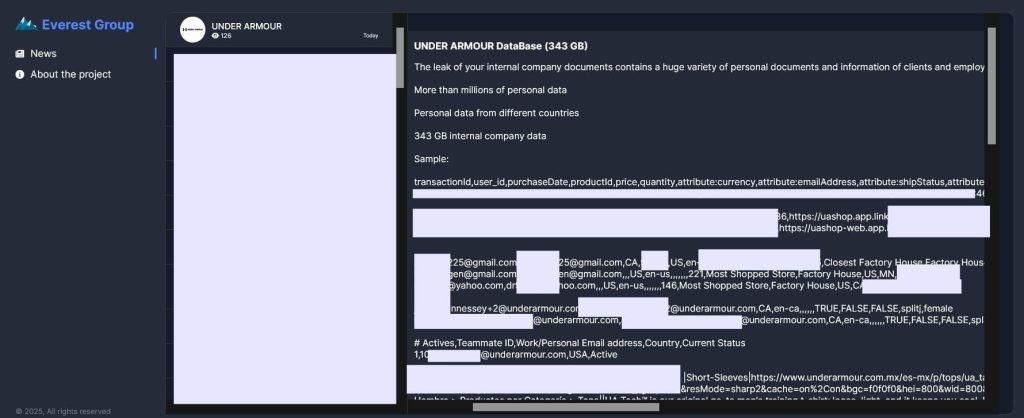
7 Day Deadline to Under Armour
Everest ransomware group has given Under Armour a seven-day deadline to make contact via Tox messenger, warning that the opportunity to respond is limited. In their message, they instructed a company representative to follow the contact steps “before time runs out,” accompanied by a countdown timer.
The group has a history of leaking data when companies refuse to engage or reject ransom demands. Previous incidents linked to Everest include the AT&T carrier website database with over half a million users’ data, 1.5 million Dublin Airport passenger records, and internal Coca-Cola employee data.
Expert Input
Shane Barney, Chief Information Security Officer at Keeper Security, commented on these claims and said that customers should take action right away. Shane explained that changing passwords on affected accounts is the first step, and those passwords need to be strong and unique.
He added that a password manager helps by creating and storing high-strength logins for every account. Shane also advised turning on Multi-Factor Authentication to add another layer of protection if logins are taken. He pointed to the value of using a dark web monitoring tool such as BreachWatch, which alerts users if exposed logins show up online.
Shane went on to say that anyone who bought products from Under Armour during the affected period should keep an eye on financial activity. If they see anything odd or simply want extra safety, they should consider cancelling the cards linked to those orders. He also warned that emails or texts connected to the incident should be treated with care, since criminals often use the situation to send convincing phishing messages.
From a business angle, Shane said that events like this show how important it is to protect the systems that hold customer and internal data. Strong access controls with privileged access management, steady monitoring and strict handling of logins help limit damage if an intruder gets in. He noted that identity-based attacks continue to be a common method for ransomware groups and that strong password habits, along with MFA, remain among the most effective defences.
Frankie Sclafani, Director of Cybersecurity Enablement at Deepwatch, shared his view on how organisations should respond to modern ransomware threats. Frankie said that reacting after an attack is no longer enough and that teams need to stay ahead of trouble through early detection. He pointed to the value of tools that study behaviour and flag activity that does not fit normal patterns, even when attackers try to hide it.
Frankie also stressed the need for strong patch habits, MFA, careful network segmentation and incident response plans that are tested in real conditions. He explained that defence has to move earlier in the process by using AI-supported insight to spot signs of trouble and cut off an attack before it grows.
What’s Next for Under Armour Customers
Hackread.com has reached out to Under Armour for comment. The breach claims made by the Everest ransomware group should be treated as allegations until the company either confirms or denies them.
In the meantime, customers are advised to monitor their accounts and banking activity, change all associated passwords, enable two-factor authentication on any accounts linked to Under Armour, and remain cautious of emails claiming to be from the company. Attackers often exploit such incidents to launch phishing campaigns disguised as breach alerts.
Update – 20/12/2025
According to Bloomberg, Under Armour is facing a proposed class action lawsuit filed by a customer after the Everest ransomware group publicly claimed responsibility for a November 2025 data breach.
The lawsuit was brought by a Texas plaintiff, Orvin Ganesh, alleging negligence and failure to safeguard personal information. The filing relies in part on the ransomware group’s public statements and sample data releases, noting that Under Armour had not formally confirmed the breach at the time the suit was filed.
According to ClassAction.org, a separate class action lawsuit was filed in Maryland by a different plaintiff, identified as Milreace Malone, against Under Armour over the same November 2025 incident.
This lawsuit alleges the company failed to implement reasonable data security measures, failed to properly encrypt sensitive information, and delayed notifying affected individuals. While both lawsuits arise from the same reported breach, they are distinct legal actions filed by different parties in different courts.
In both cases, Hackread.com’s exclusive coverage has been cited as the primary source in the lawsuit filings. However, we did not hear from Under Armour Inc.
(Photo by Kyle Bushnell on Unsplash)