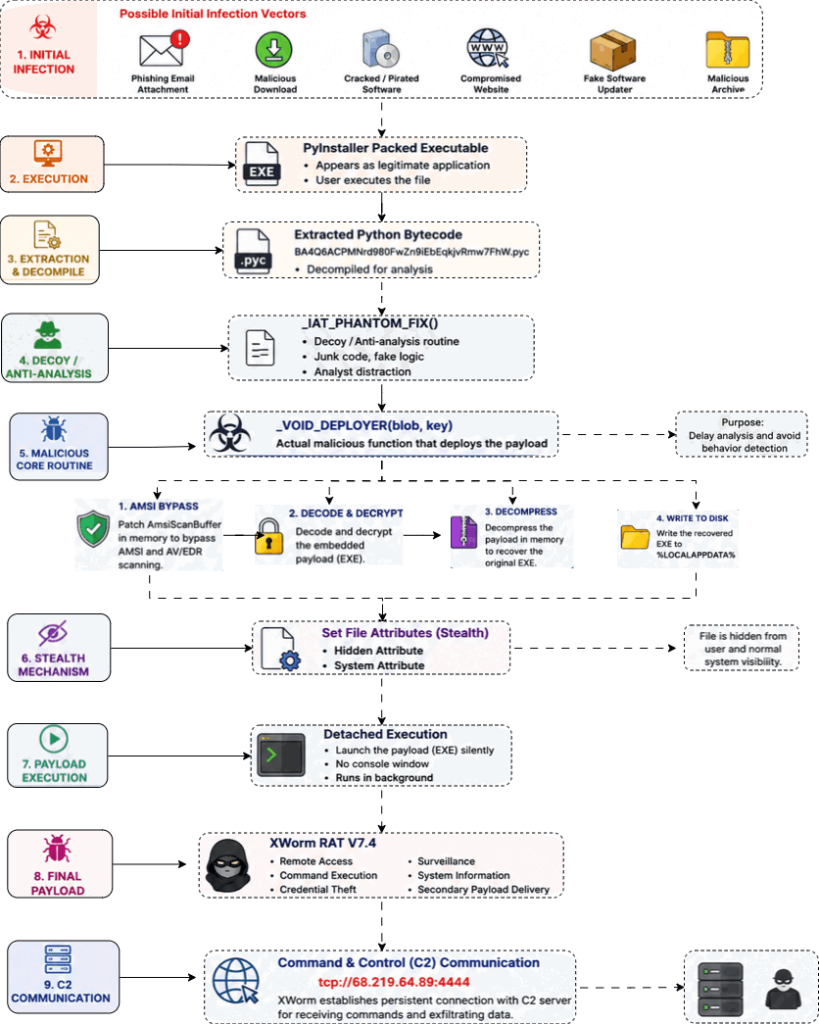
Cybersecurity researchers at Point Wild recently found a new way that cyberattackers are gaining unauthorised access to computers. The investigation, led by experts Kedar Shashikant Pandit, Prathamesh Shingare, and Amol Swami from the Lat61 Threat Intelligence Team, reveals that a common tool used by legitimate developers is being twisted by hackers to hide a nasty malware called XWorm.
Attack Details
The attack starts with a trick email or a fake software update, involving a harmless-looking file. This file is bundled with malicious code using PyInstaller, which is a tool to help programmers turn their scripts into an easy-to-run app. However, in this attack, it is converted into a delivery method for the threat.
When the victim opens the file, it runs a compiled script: BA4Q6ACPMNrd980FwZn9iEbEqkjvRmw7FhW.pyc that works in the background without showing any windows.
Point Wild’s investigation further revealed that the hackers even added a routine called _IAT_PHANTOM_FIX that researchers believe is just ‘fake’ code used to generate useless data to waste time, making it much harder for security experts to figure out what is actually happening.
Evading Security
Researchers noted in the blog post, shared exclusively with Hackread.com, that this malware is smart enough to hide from Windows security using AMSI Memory Patching that changes the computer’s memory and disables the AmsiScanBuffer, the safety guard Windows uses to scan for threats.
Breaking this guard allows XWorm to unpack its main payload safely. The payload is hidden inside the file in a scrambled format (through Base64 and SHA-512 encryption). Right after fooling the safety processes, it unscrambles itself and hides in a folder called %LOCALAPPDATA%. It also names the final file Win.Kernel_Svc_AJ8iOw.exe to make it look like a regular Windows system service and marks itself as a hidden system file so it stays invisible to the user.
Remote control and data theft
Once active, the malware (version XWorm V7.4) establishes a connection to the hackers’ remote computer using an AES secret key. It communicates with an IP address at 68.219.64.89 on port 4444 to establish this connection, which then allows the hackers to perform a range of actions, including stealing passwords, scanning through files, and turning on the webcam to spy on the user. They can also launch DDoS attacks to flood websites with traffic or drop a file called afacan313131.exe to gain full remote control of the device.
The team at Point Wild explained that threat actors are getting better at blending in with normal computer tasks to stay hidden for a long time. Dr. Zulfikar Ramzan, Chief Technology & AI Officer at Point Wild, and Head of the Lat61 Threat Intelligence Team, notes in a comment shared with us that:
“Threat actors are taking familiar malware families, like XWorm, and giving them modern packaging, inclusive of obfuscation, anti-analysis routines, AMSI bypasses, and encrypted command and control. This campaign reminds us that even known RATs become difficult to detect when the infection chain is engineered for stealth.”