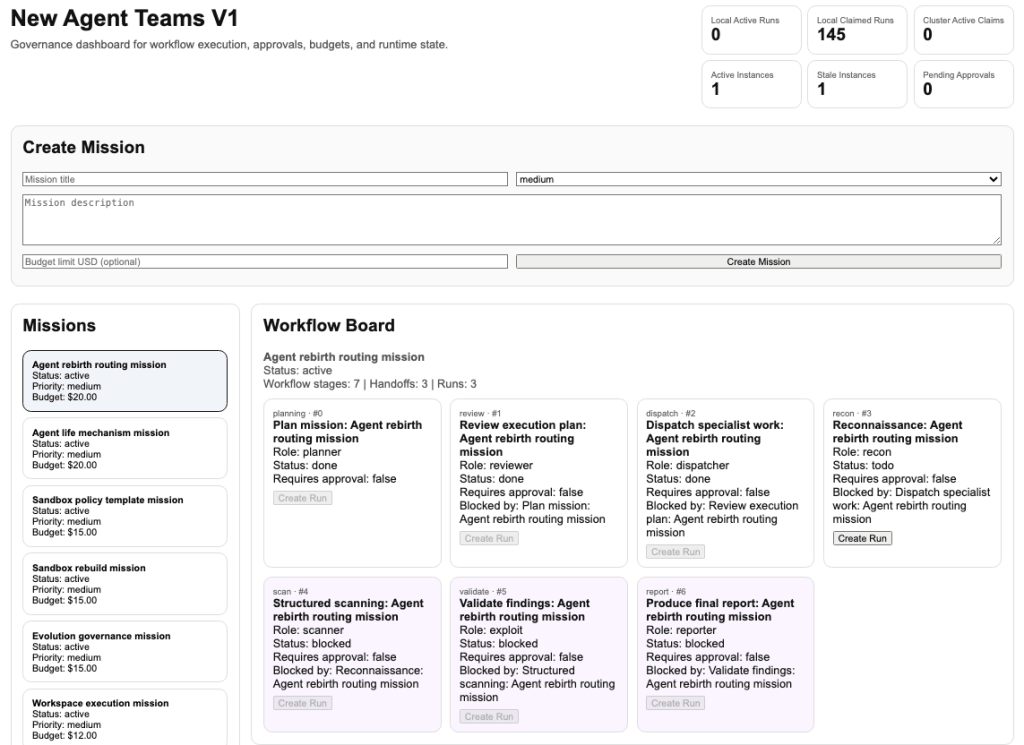
The SOCRadar Threat Research Team has discovered a massive, automated cybercrime setup linked to threat actors based in China. This operation uses a central backend called Paperclip and an agent-based workflow system known as OpenClaw.
Using these tools, the hackers run their campaigns like a business, with a step-by-step workflow that starts with Planning, followed by Review, Dispatch, Recon, Scan, Validate, and ends with a Report on the stolen data. The details of this research were shared with Hackread.com.
How the Attacks Work
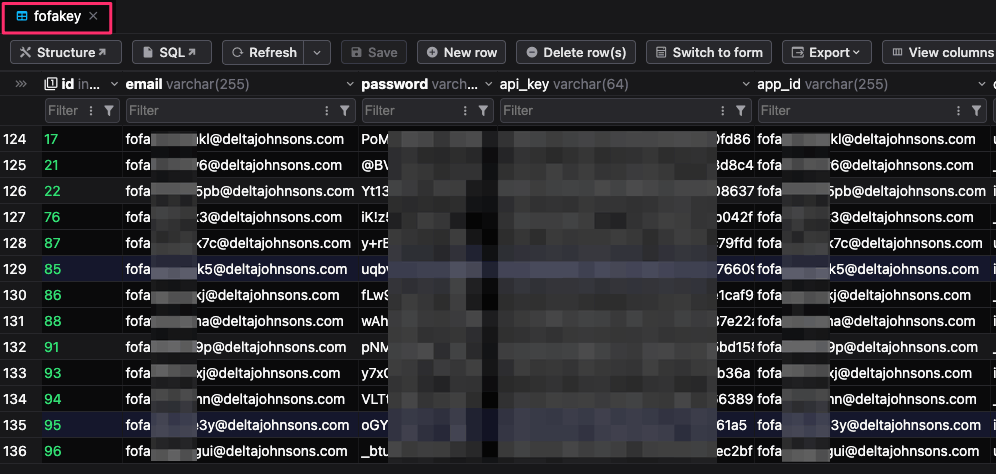
Hackers use internet mapping engines such as FOFA and 360Quake to identify the External Attack Surface (internet-facing assets). They particularly target high-value groups like fintech companies, Web3 platforms, and security vendors. To ensure their scanning remains uninterrupted, they have created thousands of automated accounts using the email pattern fofa.
This scanning helps them find systems running software with known security flaws. They prefer flaws that allow remote code execution (RCE) to gain full control over the compromised device, such as React2Shell (CVE-2025-55182) and CVE-2025-66478, and Log4Shell (CVE-2021-44228).
Researchers observed four custom Python scripts, 2.py, 3.py, 4.py, and 11.py, which help the attackers make this entire process faster and bypass security filters. This also helps them run commands on hundreds of targets at once.
“Custom Python scripts automate exploitation by executing commands such as environment variable dumps. These scripts support WAF bypass and parallel execution, enabling scalable exploitation across hundreds of targets. The primary objective is reliable remote code execution rather than simple vulnerability detection,” researchers noted in the blog post.
Stealing Data and Maintaining Persistence
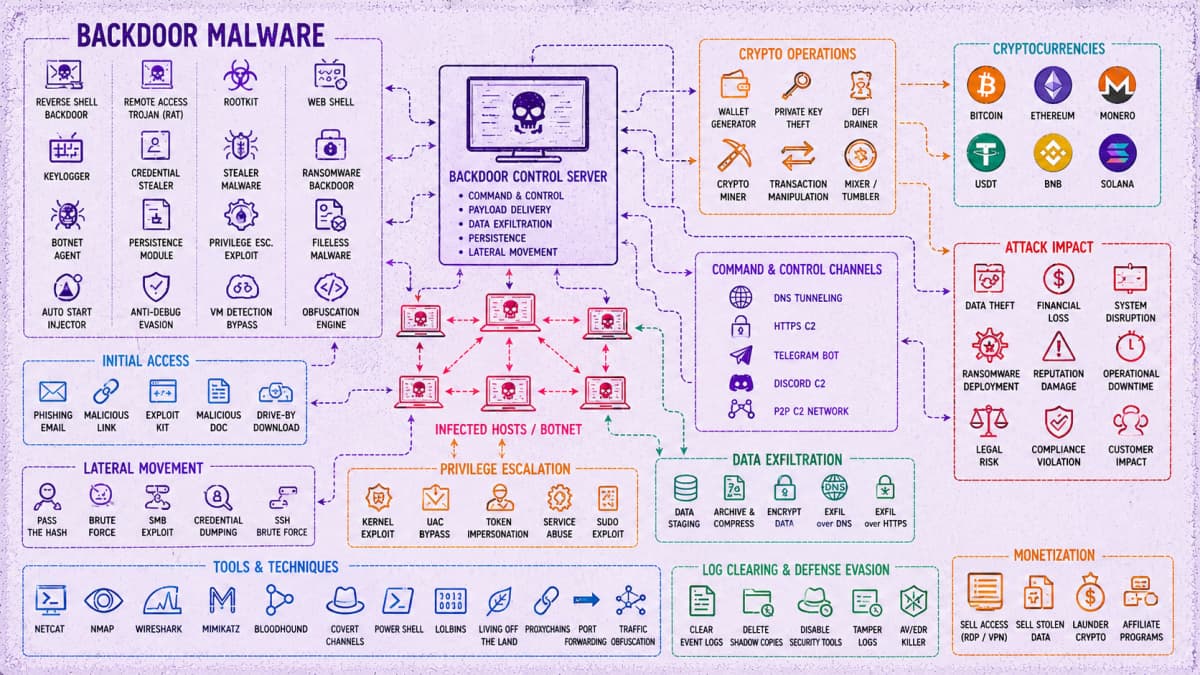
After achieving initial access, the threat actors search for sensitive data, mainly targeting AI API keys, Stripe tokens, and database credentials stored in PostgreSQL. To maintain persistence, they use several methods to ensure they stay hidden, like deploying Cloudflare tunnels via cf-client, P2P clients named mayun, and backdoors identified in logs as d2 and pl.
The group also uses a fileless execution chain using commands that feed web content directly into Node.js to run malicious code in the system’s memory without saving any files to the disk. This makes malware detection much more difficult.
The Scale of the Operation
This is a very large operation. The hackers’ own logs show around 45,000 attack attempts. Their database shows they have placed the d2 backdoor on 3,981 hosts and the pl backdoor on 1,393 hosts. They also managed 900 webshell implants and are tracking nearly 22,000 cryptocurrency addresses.
For context, d2 and pl are two custom backdoor implants used by the attackers to maintain access to the compromised system.
“The operation is coordinated through a centralised backend,” the report explains, which helps the group manage and enrich stolen data. The hackers use blockchain intelligence APIs such as OKLink and Tatum to monitor nearly 22,000 cryptocurrency addresses. They also use automated scripts to validate stolen Stripe keys by checking for active accounts with available balances. This organised approach allows the threat actors to immediately prioritise the most profitable targets.