Cybercriminals have found a way to bypass security controls by using your work schedule against you, reveals a new report from Fortra Intelligence and Research Experts (FIRE). The report, shared with Hackread.com, shows hackers are now actively exploiting calendar invites to hijack accounts.
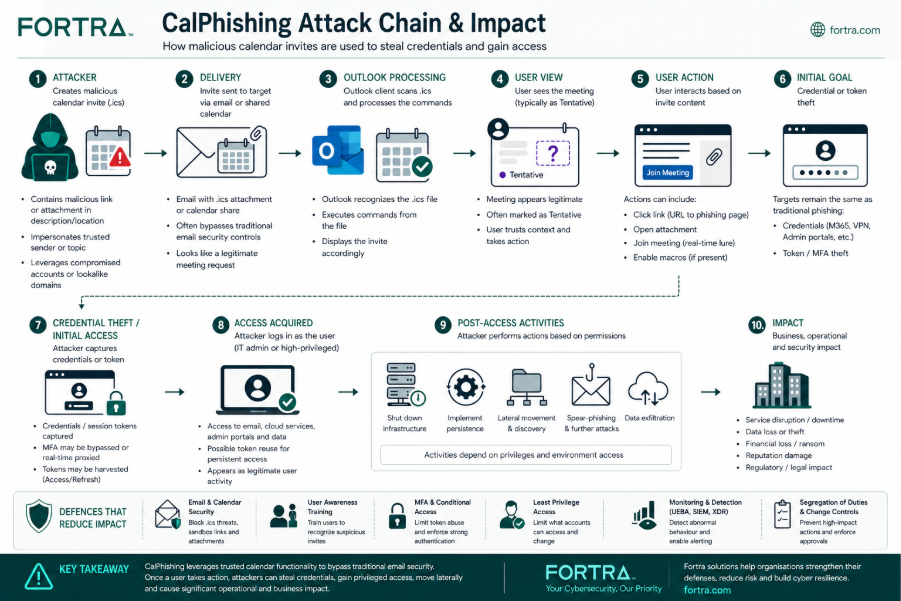
The Attack Chain
This campaign, which researchers identified as active in early 2026, uses a method called CalPhishing (Calendar Phishing) in which scammers send an iCalendar (.ics) file that places a meeting directly on a victim’s calendar, without the person ever opening or even seeing the original email.
The process starts with an email that appears to be an urgent administrative alert. Common subject lines include : Domain Renewal Failed or Reminder for Signature – Vendor Information Verification.
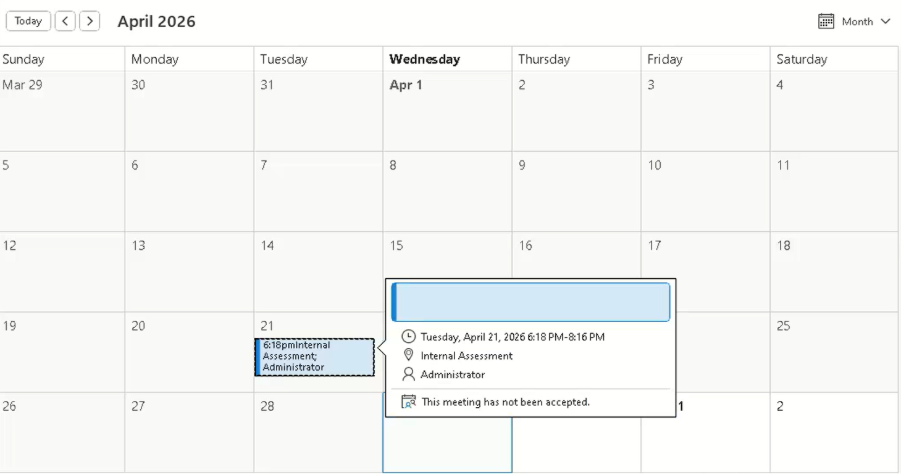
As soon as the Outlook app processes this .ics file, it automatically creates a ‘tentative’ meeting. Since this meeting is now on your schedule, you will start getting official notifications and reminders on your phone or computer. After the invite is on the calendar, hackers abuse several fields to trick you:
- SUMMARY: Creates a fake sense of urgency.
- LOCATION: Often references an attached file to seem official.
- DESCRIPTION: Contains the main scam message and instructions.
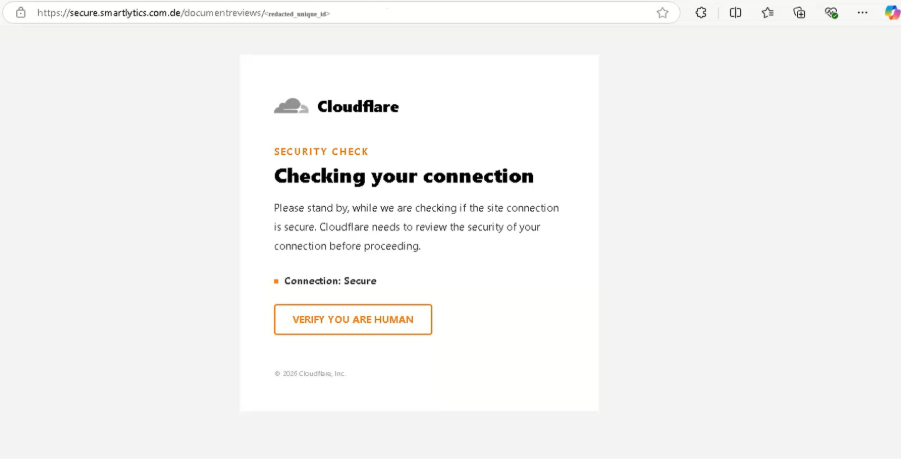
If a user opens the meeting, they see an HTML file that mimics an admin portal. Clicking it starts a chain of redirects through Cloudflare to hide from security scanners.
Two-Fold Lures
Researchers identified two specific lures. The first mimics Microsoft 365 alerts about a domain renewal, leading to a fake GoDaddy page. The second is a request for a digital signature on an invoice, typically using a fake DocuSign page.
Further probing revealed that this campaign uses a technique called ConsentFix, aka device code phishing. In this technique, instead of just stealing a password, the hackers can steal a session token.
They also assessed that hackers are likely using the EvilTokens phishing kit (sold on Telegram) that helps them automate this entire process. Hackers can infiltrate an account even if the user has multi-factor authentication (MFA) enabled, simply by stealing these tokens. Once inside, they can cause utter chaos, like shutting down systems or stealing private data.
Persistence and AI Automation
The most worrying part is how the threat stays active. Standard tools often miss these invites because .ics files are generally trusted.
“A meeting request is used as the primary interaction point… a soft delete or move to junk does not remove the meeting entry from the calendar itself,” the researchers noted in the blog post.
The FIRE team believes hackers are using AI automation to send these invites at a high volume. Because the meeting remains on the calendar unless a Hard-Delete is performed, victims remain vulnerable long after the initial email is gone.